Introduction
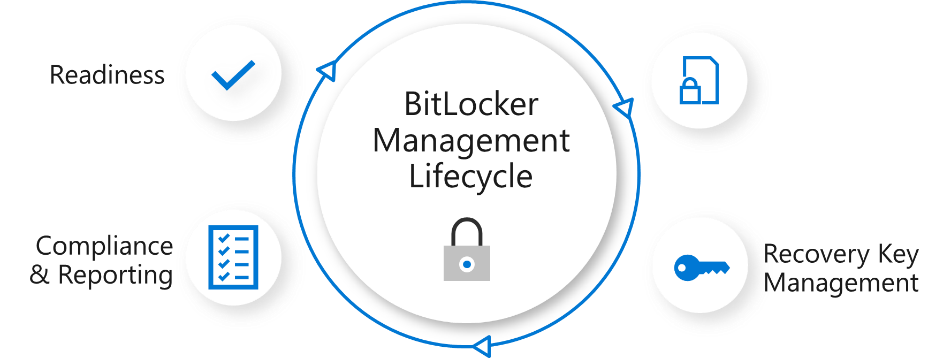
Microsoft BitLocker Administration and Monitoring (MBAM) is the ability to have a client agent (the MDOP MBAM agent) on your Windows devices to enforce BitLocker encryption including algorithm type, and to store the recovery keys in your database, securely. It includes reporting, key rotation, compliance and more.
The following blog post from Microsoft details their future direction with regard to BitLocker Management and is a must read. They’ve since written a new blog about the subject here.
The purpose of this blog post is to gather together guides and videos I’ve created since Bitlocker Management appeared as a feature in Configuration Manager Technical Preview version 1905 and onwards to it’s release in production in Configuration Manager version 1910 (Current Branch).
Videos
- BitLocker management – Part 1 Initial setup
- BitLocker management – Part 2 Deploy portals
- BitLocker management – Part 3 Customize portals
- BitLocker management – Part 4 Force encryption with no user action
- BitLocker management – Part 5 key rotation
- BitLocker management – Part 6 Force decryption with no user action
- BitLocker management – Part 7 Reporting and compliance
- BitLocker management – Part 8 Migration
- BitLocker management – Part 9 Group Policy settings
- BitLocker management – Part 10 Troubleshooting
Guides
- Getting started with On-premises BitLocker management using SCCM
- How does Key Rotation work in MBAM integrated with SCCM ?
- How can you use the Self Service feature when MBAM is integrated within SCCM?
- How can you use the Help Desk feature when MBAM is integrated within SCCM?
- A quick look at reporting in MBAM integrated within Microsoft Endpoint Manager Configuration Manager
- How can I get BitLocker Recovery Keys from the ConfigMgr database
- How to fix: “Unable to find suitable Recovery Service MP. Marking policy non-compliant”
- How to use Full Disk Encryption in a task sequence in Configuration Manager 1910
- Full disk encryption (in ConfigMgr 1910) – a closer look using real hardware
- Download the Windows 10 version 1909 ADMX templates
- How to use the Central Store for Windows 10 ADMX files
- How can we utilize the Bitlocker Management feature during OSD with Endpoint Manager
- using BitLocker Management in ConfigMgr and do OSD, read this !
- Hotfix available for ConfigMgr version 2103 to solve policy storm issues caused by Invoke-MbamClientDeployment.ps1
Microsoft Docs
- What’s new in 1910 – https://docs.microsoft.com/en-us/configmgr/core/plan-design/changes/whats-new-in-version-1910
- Plan – https://docs.microsoft.com/en-us/configmgr/protect/plan-design/bitlocker-management
- Deploy – https://docs.microsoft.com/en-us/configmgr/protect/deploy-use/bitlocker/deploy-management-agent
- Encrypt recovery data – https://docs.microsoft.com/en-us/configmgr/protect/deploy-use/bitlocker/encrypt-recovery-data
- Install the MBAM portals – https://docs.microsoft.com/en-us/configmgr/protect/deploy-use/bitlocker/setup-websites
- Migration – https://docs.microsoft.com/en-us/configmgr/protect/deploy-use/bitlocker/deploy-management-agent#migration-considerations
- Planning for MBAM Group Policy – https://docs.microsoft.com/en-us/microsoft-desktop-optimization-pack/mbam-v25/planning-for-mbam-25-group-policy-requirements
- MBAM ADMX – https://docs.microsoft.com/en-us/microsoft-desktop-optimization-pack/solutions/how-to-download-and-deploy-mdop-group-policy–admx–templates
- Download the ADMX – v.2.8
Note: BitLocker Management integrated in 1910 requires a https enabled management point. If you’d like help to configure PKI then see my links below. Please keep in mind that since I blogged this, Microsoft Endpoint Manager 2002 was released and it contains updates to the BitLocker Management feature (and requirements) shown here.
- The BitLocker recovery service requires HTTPS to encrypt the recovery keys across the network from the Configuration Manage client to the management point. There are two options:
- HTTPS-enable the IIS website on the management point that hosts the recovery service. This option only applies to Configuration Manager version 2002.
- Configure the management point for HTTPS. This option applies to Configuration Manager versions 1910 or 2002.
For more information, see Encrypt recovery data.
Setting up PKI in a lab
- Part 1 – Introduction and server setup
- Part 2 – Install and do initial configuration on the Standalone Offline Root CA
- Part 3 – Prepare the HTTP Web server for CDP and AIA Publication
- Part 4 – Post configuration on the Standalone Offline Root CA
- Part 5 – Installing the Enterprise Issuing CA
- Part 6 – Perform post installation tasks on the Issuing CA
- Part 7 – Install and configure the OCSP Responder role service
- Part 8 – Configure AutoEnroll and Verify PKI health
Convert ConfigMgr from HTTP to HTTPS
- How can I configure System Center Configuration Manager in HTTPS mode (PKI) – Part 1
- How can I configure System Center Configuration Manager in HTTPS mode (PKI) – Part 2



Great stuff as always Niall!
Pingback: Learn about MBAM integration in Microsoft Endpoint Configuration Manager version 1910 | just another windows noob ?
Pingback: Learn about MBAM in Microsoft Endpoint Configuration Manager version 1910 – part 6 decrypting drives | just another windows noob ?
Pingback: Learn about MBAM in Microsoft Endpoint Configuration Manager version 1910 – part 7 Reporting and compliance | just another windows noob ?
Pingback: Learn about MBAM in Microsoft Endpoint Configuration Manager version 1910 – part 8 Migration | just another windows noob ?
Yeap, this is one to keep handy. Thanks again…
Pingback: System Center Ocak 2020 Bülten – Sertaç Topal
Pingback: Learn about Bitlocker Management in Microsoft Endpoint Configuration Manager version 1910 – part 9 Group Policy | just another windows noob ?
Pingback: Learn about Bitlocker Management in Microsoft Endpoint Configuration Manager version 1910 – Part 2, configure portals | just another windows noob ?
Pingback: Learn about Bitlocker Management in Microsoft Endpoint Configuration Manager version 1910 – part 3 customize the portals | just another windows noob ?
Pingback: Learn about Bitlocker Management in Microsoft Endpoint Configuration Manager version 1910 – part 4 Enforce encryption | just another windows noob ?
Pingback: Learn about Bitlocker Management in Microsoft Endpoint Configuration Manager version 1910 – part 5 key rotation | just another windows noob ?
Pingback: Learn about Bitlocker Management in Microsoft Endpoint Configuration Manager version 1910 – part 6 forcing decryption | just another windows noob ?
Pingback: Full disk encryption (in ConfigMgr 1910) – a closer look on real hardware | just another windows noob ?
Hi Niall, those are amazing tutorials, thank you!
BTW, have you seen a problem where the registry key MDOPBitLockerManagement is never populated with the corresponding MBAM entries? The MDOP is installed successfully, I see no errors in the logs, but the client never starts encrypting and I guess this is the reason. This is happening with a few clients out of 200.
Thanks a lot!
Marcelo Viegas
hi Marcelo,
thanks for the thanks, so can you go into more detail about what you are seeing exactly ? are you saying the reg keys don’t get created at all ? were these devices ever managed by MBAM ? do they have the correct client version and the MDOP agent installed ?
Hi Niall,
Thank you very much for detailed guide on Bitlocker management.
I need to implement Bitlocker on around 5k (Win10 1909) devices using ConfigMgr 1910. All the pre-requisites like https enabled MP and TPM are installed/configured.
we have two MBAM policies, one for desktop (TPM only) and another for laptop (TPM + PIN), both policies having identical settings except below,
• OS Drive encryption settings (for desktop chassis):
– Allow Bitlocker without a compatible TPM (requires a password) – Do Not Allow
– Select Protector for a operating system drive – TPM only
• OS Drive encryption settings (for laptop chassis):
– Allow Bitlocker without a compatible TPM (requires a password) – Allow
– Select Protector for a operating system drive – TPM and PIN
As you suggested, DCM baseline also created to start encryption without end user intervention, and I can see, those two registry keys being created on endpoint.
However for unknown reason, automatic encryption is not working and I see no error in MBAM event logs and SCCM Bitlocker logs as well. We have no MBAM group policy settings, which may conflict with SCCM policy.
If I trigger encryption manually, that encrypts the disk with settings from Bitlocker policy and reports the state as ‘compliant’ as well.
Not sure, what I’m missing here. any help would be appreciated….!!!
hi there,
first of all the DCM baseline to ‘force encryption’ must be set BEFORE the computers get bitlocker encrytpion policies,
have you verified that ?
Thanks Niall for prompt response..
Yes, I can confirm that, DCM policy enforced before bitlocker policy.. just running out-of ideas now 🙁
are you verifying on real hardware ? did you make sure that the TPM shows up in the device manager ? is it enabled in the bios…
Yes, I’ve 2 physical machines where TPM is enabled in BIOS and appears in device manager as well..
I am also having the similar issue. Do you think any gpo policy might be interfering with writing those policy from SCCM?
it’s possible, so to find out, make sure your bitlocker management computers are in an OU that is not targeted by any MDOP related GPO for testing.
Only GPO policy for MDOP I have is the one to show which number to call if the user get the Bitlocker screen. Its from one your tutorial.
I am also having the similar issue. Do you think any gpo policy might be interfering with writing those policy from SCCM?
This is very detailed and explanatory post and will come in handy for anyone looking to integrate Bitlocker Management with SCCM . Big Thank you !
Would anyone be able to share what the client behaviour is for windows endpoints where they were already Bitlocked and the backend was moved to SCCM . Will they still get pop up to encrypt . Will all client policies be reapplied ?
take a look at my reply here to a similar question, hopefully it answers it for you
https://www.windows-noob.com/forums/topic/16726-on-premises-bitlocker-management-using-system-center-configuration-manager/?do=findComment&comment=68195
Pingback: How can we utilize the Bitlocker Management feature during OSD with Endpoint Manager | just another windows noob ?
Pingback: Troubleshooting BitLocker Management in ConfigMgr – Part 1. Server side | just another windows noob ?
Got a odd question does the configuration manager client install MDOP MBAM if you are using it for your Bitlocker escrow database? I have disabled all of my MDOP MBAM Steps in the task sequence and have no deployments of it but it is still being installed on the computers. I removed the client and MDOP MBAM from my computer and resinstalled the client and back MDOP MBAM came. I cant seem to figure out if this is something that naturally happens and is expected or if I should not have the client installed as it is deprecated.