Introduction
I’m currently blogging about a series of DEM in 20 webinars from 1E, you can find each episode that I’ve blogged about (including this one) below:
- Episode 1. How to find and fix Slow Endpoints
- Episode 2. That crashy app
- Episode 3. Dealing with annoying admin requests
- Episode 4. That Change Management Success Rate Struggle
- Episode 5. Will Printer Audits continue to exist? <- you are here
- Episode 6. Are non compliant devices dangerous ?
In today’s blog post I’ll cover a topic that’s very relevant considering the printer patching mess that was so public recently, namely: Will Printer Audits continue to exist?
Many companies had to deal with the recent PrintNightmare (CVE-2021-34527) problem and the patching mess that ensued. Today’s blog post will focus on the details of the vulnerability and based on those details and resolution advice learn how Tachyon can help you in real time search for registry keys, set registry keys to a specific value or disable services and thereby help to secure your enterprise.
Companies everywhere print content. It’s a normal part of every day business and they’ve been doing that for years, but we do need to ask ourselves the question, do we really need a printer, or we should consider if we are going to move towards a more eco-friendly solution.
In this DEM in 20 video, guest Gary Edwards who is a Senior Solutions Engineer at 1E with 30 years of experience, talks us through how Tachyon can help solve this mess.
What is PrintNightmare?
Discovered by researchers at QiAnXin, PrintNightmare (CVE-2021-34527) is a vulnerability which affects the Microsoft Windows Print Spooler Service. It has the potential to enable cyber-attackers to gain complete control of an affected system.
“PrintNightmare is a hot new target for ransomware groups. It will allow these groups to quickly go from a single compromised workstation, to access to the whole network. Thus far, Microsoft’s patches have failed to fully address the problem. As such, the consensus is that organisations should disable print services on all systems where it isn’t needed.”
Source:www.redscan.com
When Microsoft releases a patch, you definetly want to patch your environment to keep your IT environment secure. In the case of PrintNightmare, the vulnerability all revolved around a service running on Windows computers (both desktop and servers) called the Spooler service. It’s been there in Windows for years, it’s always on by default and doesn’t interact with users, it just waits for a user to print and then it comes alive.
A few months ago, the Microsoft Security Response center got word about cyber security researchers who identified a hole or bug, to allow you to exploit the print spooler service and gain full control of a computer, remotely. Responding to this on July 1st, Microsoft released the following CVE-2021-34527 explaining the implications of this security vulnerability.
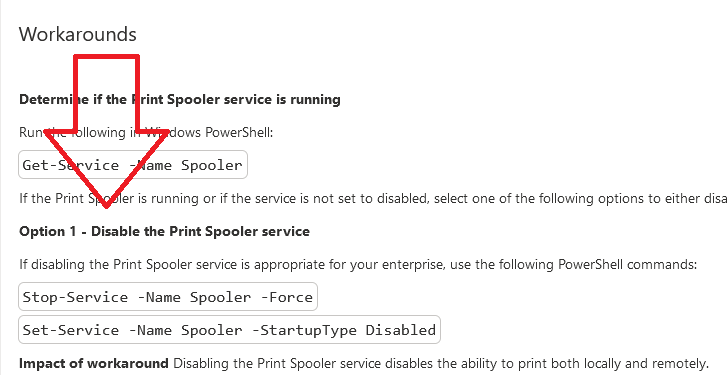
It included additional details about setting registry key values on the endpoint and it also added 2 workarounds, including disabling the print spool service.
“In addition to installing the updates, in order to secure your system, you must confirm that the following registry settings are set to 0 (zero) or are not defined (Note: These registry keys do not exist by default, and therefore are already at the secure setting.), also that your Group Policy setting are correct (see FAQ):”
-
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Printers\PointAndPrint
-
NoWarningNoElevationOnInstall = 0 (DWORD) or not defined (default setting)
-
UpdatePromptSettings = 0 (DWORD) or not defined (default setting)
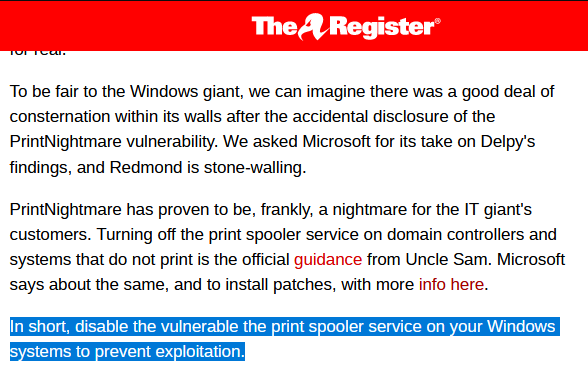
Unfortunately, not long after Microsoft released the patch, many tech blogs such as The Register were talking about the failure of the patch and the advice they offered was to instead, disable print services completely to avoid exploitation.
 But this advice was pretty severe, what would it mean for Enterprises, what would it mean for consumers, for schools. Also, how would you go about doing that quickly and safely in an Enterprise that had say 80,000 endpoints or more.
But this advice was pretty severe, what would it mean for Enterprises, what would it mean for consumers, for schools. Also, how would you go about doing that quickly and safely in an Enterprise that had say 80,000 endpoints or more.
Securing your network with Tachyon
Tachyon has various capabilities to assist admins with this very problem, so let’s take a closer look at how you can solve and remediate these issues. We’ll start by using Tachyon Explorer to search for registry keys.
Locating registry keys
In Tachyon Explorer, in the I want to know search field, type the search term registry and then selecting what are all the keys under the registry key <hive> <subkey> from the list of choices.
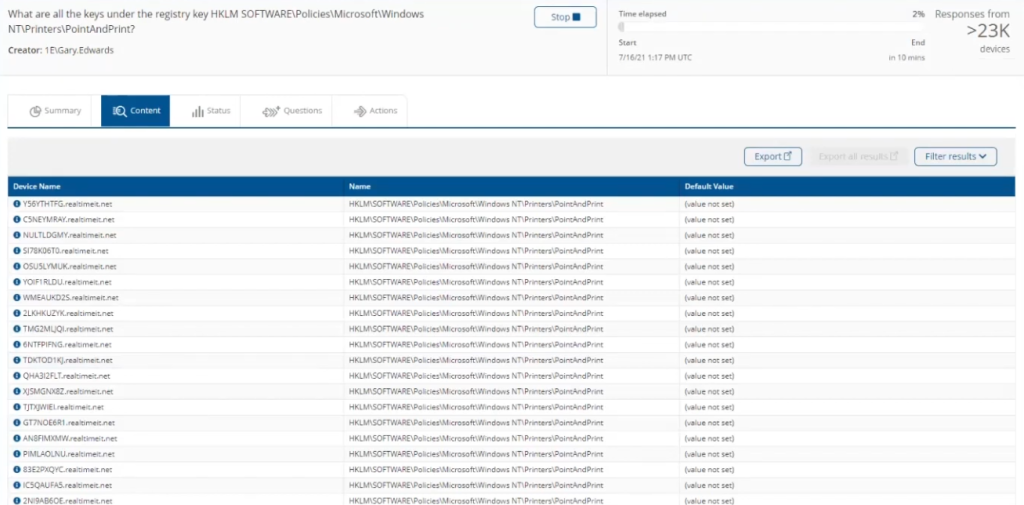
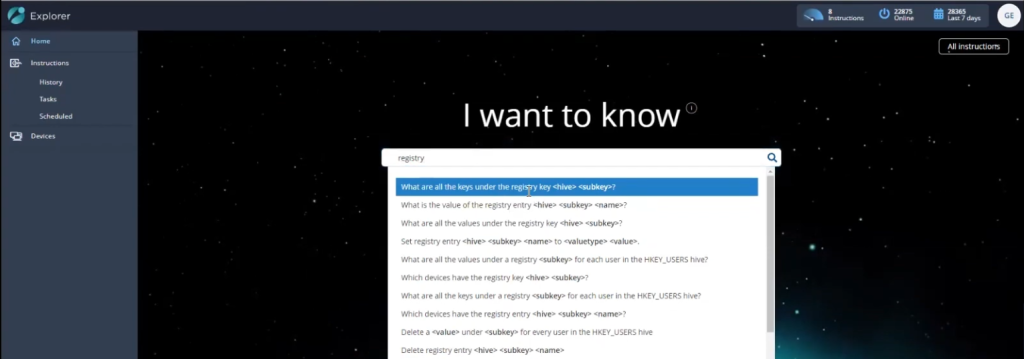 That brings up another option to enter the hive and subkey values and in this example finds results instantaneously on 22,886 endpoints out of 36,807 devices.
That brings up another option to enter the hive and subkey values and in this example finds results instantaneously on 22,886 endpoints out of 36,807 devices.
 Below is some of the data that is displayed for those 23,000 endpoints. It shows you the registry key on the device and more importantly in the Default Value column, that the registry key is not set, and that is critical information as that is the advice that Microsofts CVE explains needs to be resolved (setting those registry keys).
Below is some of the data that is displayed for those 23,000 endpoints. It shows you the registry key on the device and more importantly in the Default Value column, that the registry key is not set, and that is critical information as that is the advice that Microsofts CVE explains needs to be resolved (setting those registry keys).
Setting registry keys
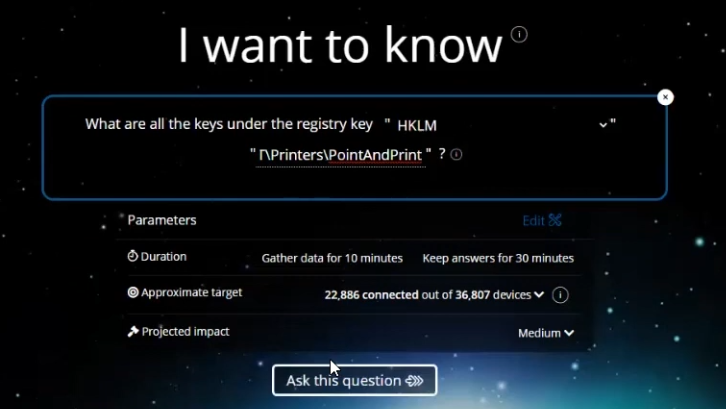
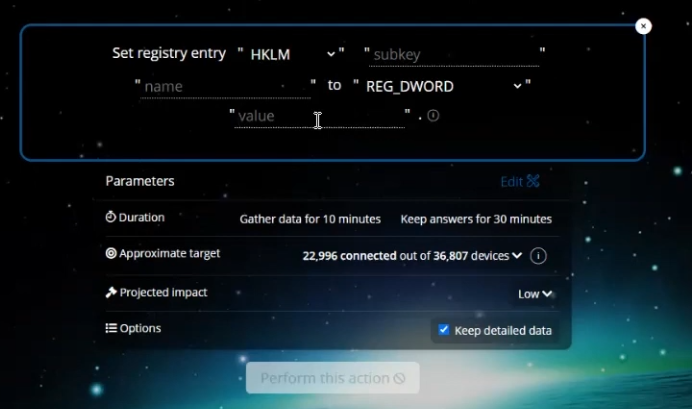
One of the requirements of the first part of the CVE was that we had to set registry keys on affected endpoints. With Tachyon, it’s easy. Here’s how to do it. In Tachyon Explorer, in the I want to know search field, type the search term registry and then select Set registry entry <hive> <subkey> <name> to <valuetype> <value> from the list of choices.
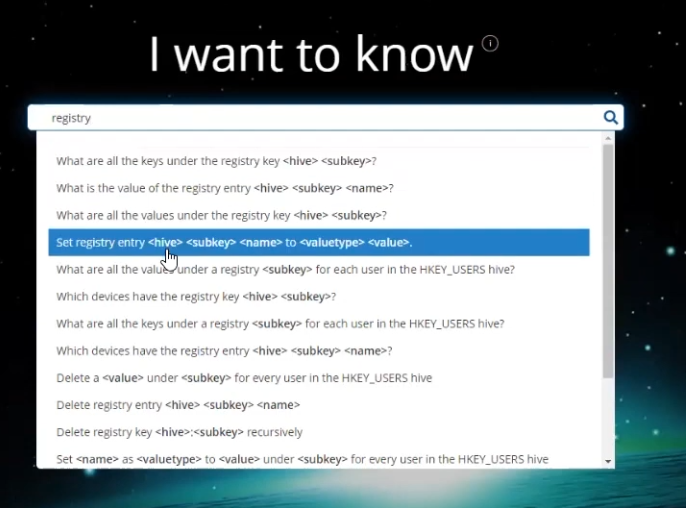 That will bring up a new screen allowing you to set a registry entry as shown below. Fill in the values as recommended in the CVE.
That will bring up a new screen allowing you to set a registry entry as shown below. Fill in the values as recommended in the CVE.
 Alternative ways of doing this could involve using Tachyon Guaranteed State to set and maintain this state on all endpoints, creating a Group Policy incorporating PowerShell scripts or VBS scripts to set these keys on thousands of endpoints, or (if you have ConfigMgr) use Configuration Baselines to do it.
Alternative ways of doing this could involve using Tachyon Guaranteed State to set and maintain this state on all endpoints, creating a Group Policy incorporating PowerShell scripts or VBS scripts to set these keys on thousands of endpoints, or (if you have ConfigMgr) use Configuration Baselines to do it.
Stopping services
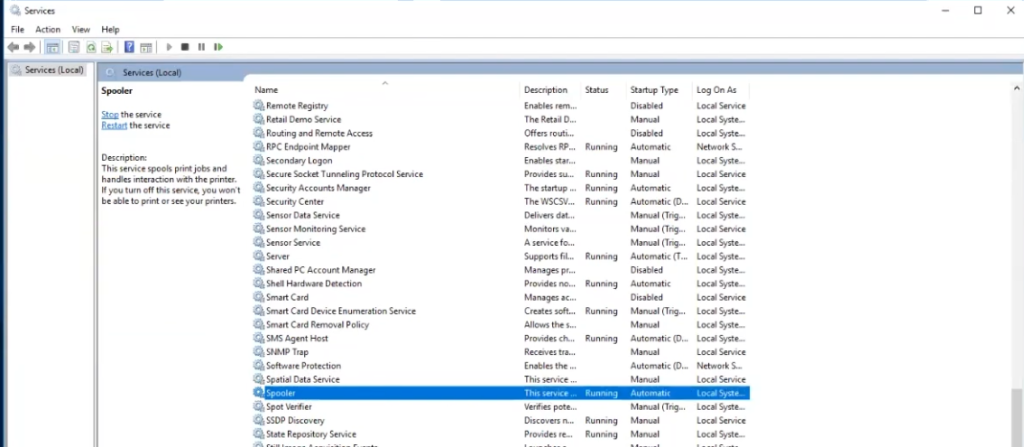
As explained in the CVE, there were 2 workarounds, one of which included disabling the print spooler service.
Below you can see what the printer service looks like when it’s in a running state on an endpoint.
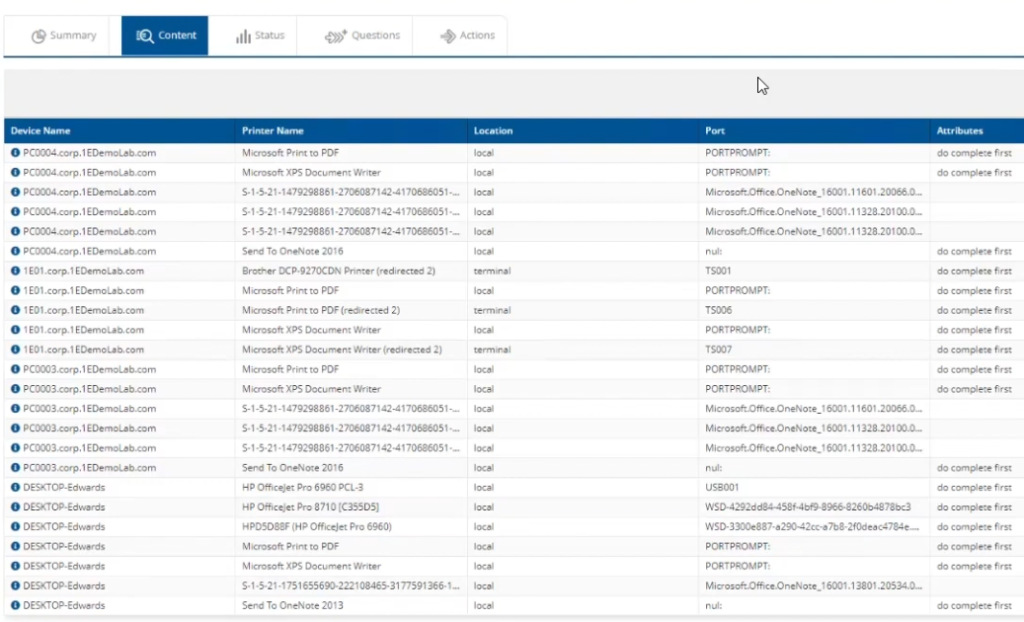
 So let’s look at how to do that. In Tachyon Explorer, in the I want to know search field, type the search term printers and then select List information about printers attached physically that may be shared from the list of choices available in the drop down menu shown.
So let’s look at how to do that. In Tachyon Explorer, in the I want to know search field, type the search term printers and then select List information about printers attached physically that may be shared from the list of choices available in the drop down menu shown.
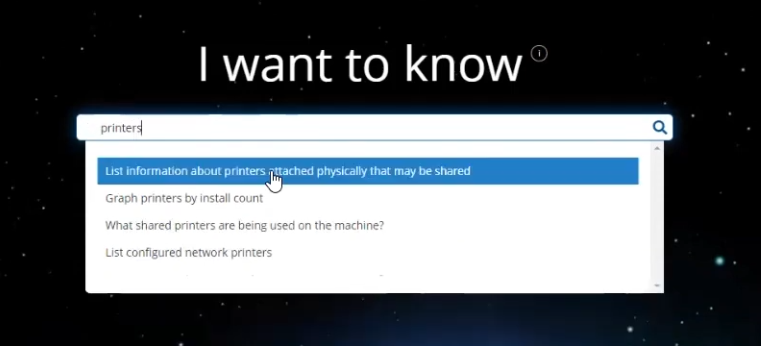 This allows you to audit what’s going on in your environment.
This allows you to audit what’s going on in your environment.
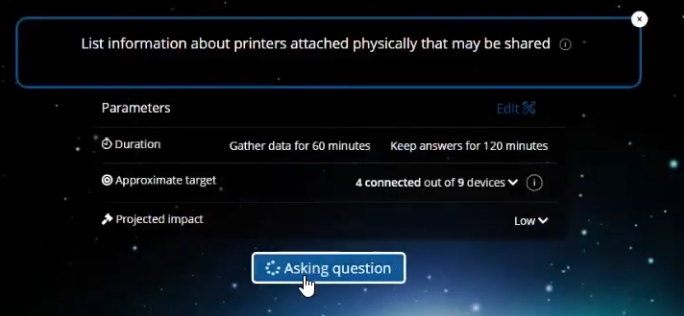 This produces a list of vulnerable devices.
This produces a list of vulnerable devices.
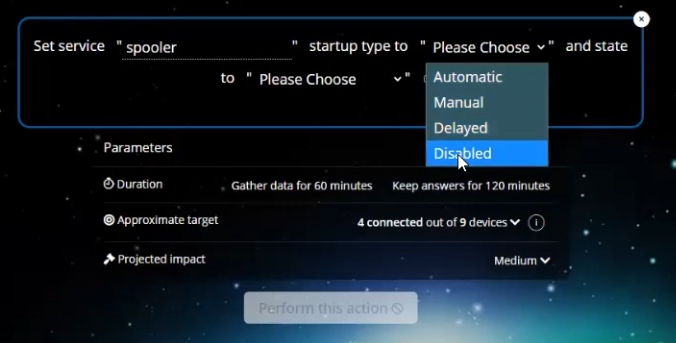
 In order to change the service state from running to stopped and disabled do as follows. In Tachyon Explorer search for servicename and in the results field select Change service <servicename> and its dependencies to <state> state.
In order to change the service state from running to stopped and disabled do as follows. In Tachyon Explorer search for servicename and in the results field select Change service <servicename> and its dependencies to <state> state.
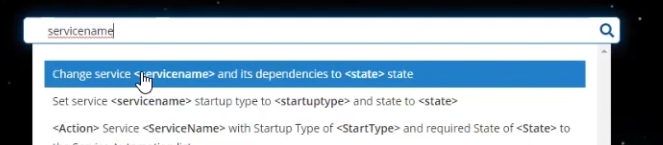 This in turn allows you to enter the spooler service name and select the startup type to Disabled from the options available.
This in turn allows you to enter the spooler service name and select the startup type to Disabled from the options available.
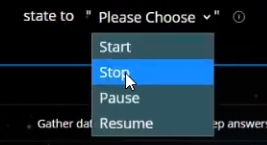
Not only that but you can set the current state to Stop to stop currently running services.
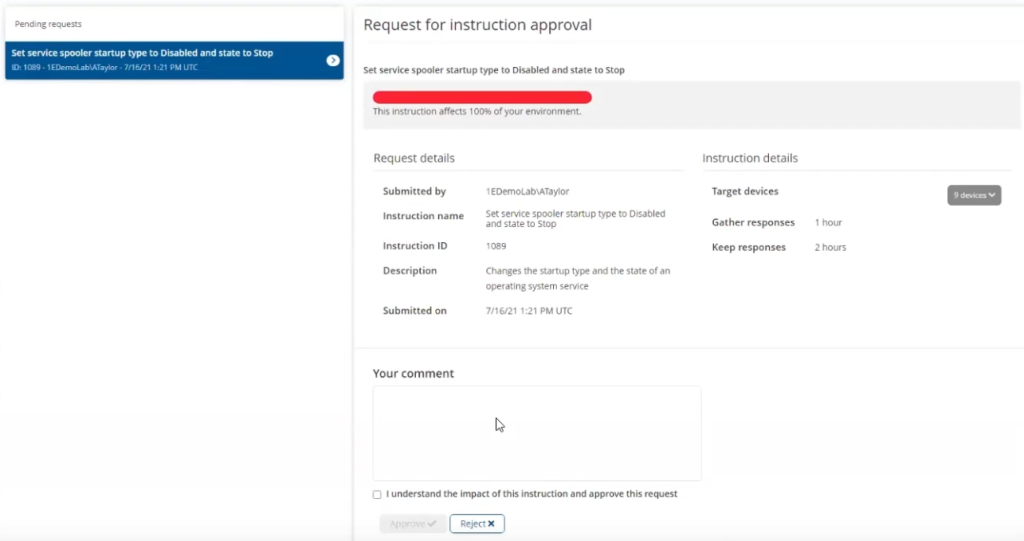
An integral part of the Tachyon experience is the ability to enable the approval of admin actions, this is to avoid a rogue admin doing unwanted actions.
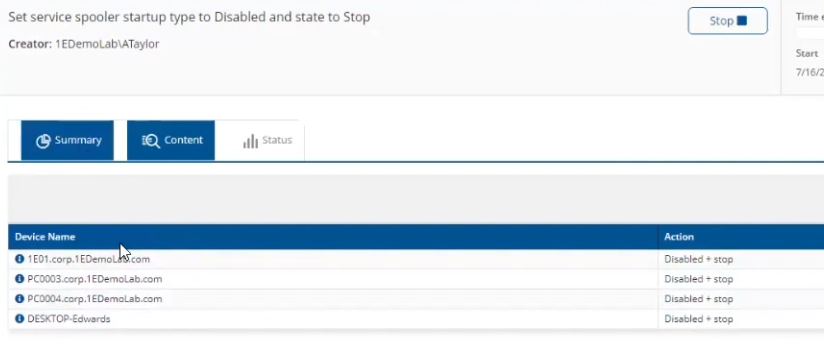
After approval, we can see that the rule has run and that the actions are completed.
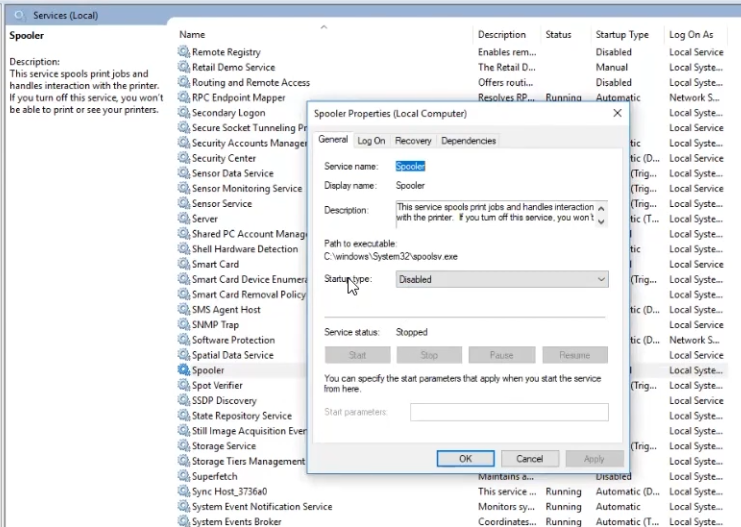
A quick remote in to any of those devices will show the service is indeed stopped and the startup type is disabled.
Maintaining desired state
To stop people from coming in and starting the service on their own computer you’d want to have a policy to stop them from doing so. The easiest way would be to make sure users are all standard users but if you cannot do that, you can use Tachyon Guaranteed State to force compliance. Let’s take a look at that. In the dashboard below you can easily see the compliance or non-compliance in your enterprise.
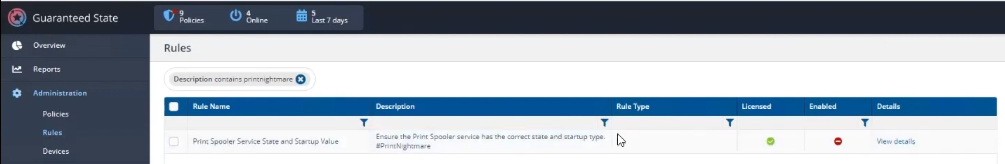
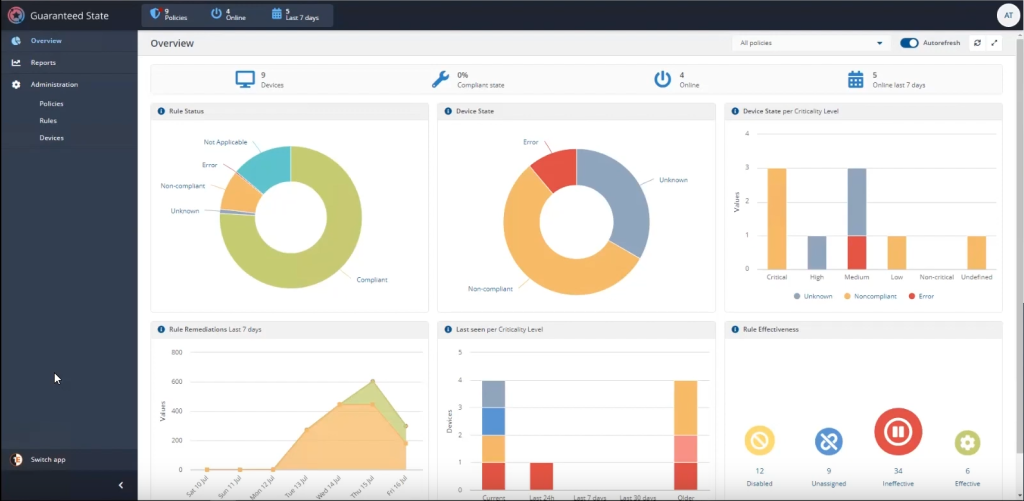 You can also create rules to maintain the state and startup value that you want, for example to force the spooler service to stopped. This particular rule is set to a rule type of Fix meaning it will continually resolve non-compliant endpoints.
You can also create rules to maintain the state and startup value that you want, for example to force the spooler service to stopped. This particular rule is set to a rule type of Fix meaning it will continually resolve non-compliant endpoints.
But setting a rule like this means no one can print in your network as the print spooler service will be disabled and stopped. To enable the ability to print when needed 1E have partnered with ServiceNow to enable users to request the ability to print on demand.
Conclusion
Security issues occur all the time in today’s digital landscape, and issues such as remote code execution and user elevation need to be addressed as soon as possible. The recent PrintNightmare issue highlighted how admins need to figure out which endpoints in their environment are affected and how to quickly resolve the problem.
Tachyon Explorer gives admins the power to quickly verify registry settings, or to change them as appropriate, and do it all in real time with auditing and approval. Using Tachyon Guaranteed State they can enforce the desired policy so that the vulnerabilities are removed.