Introduction
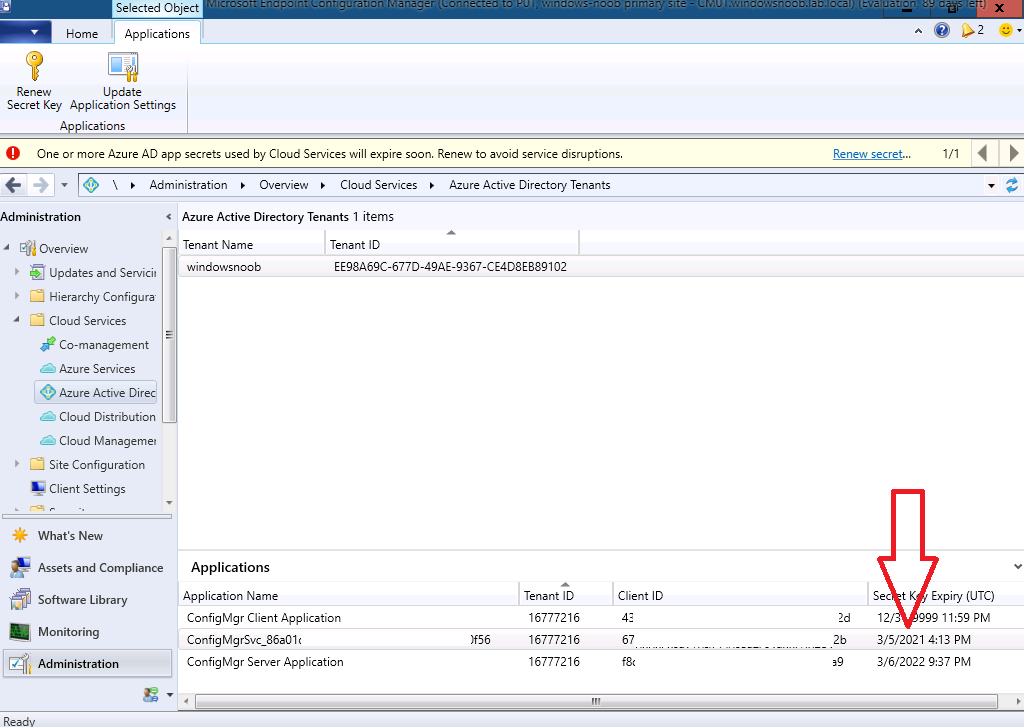
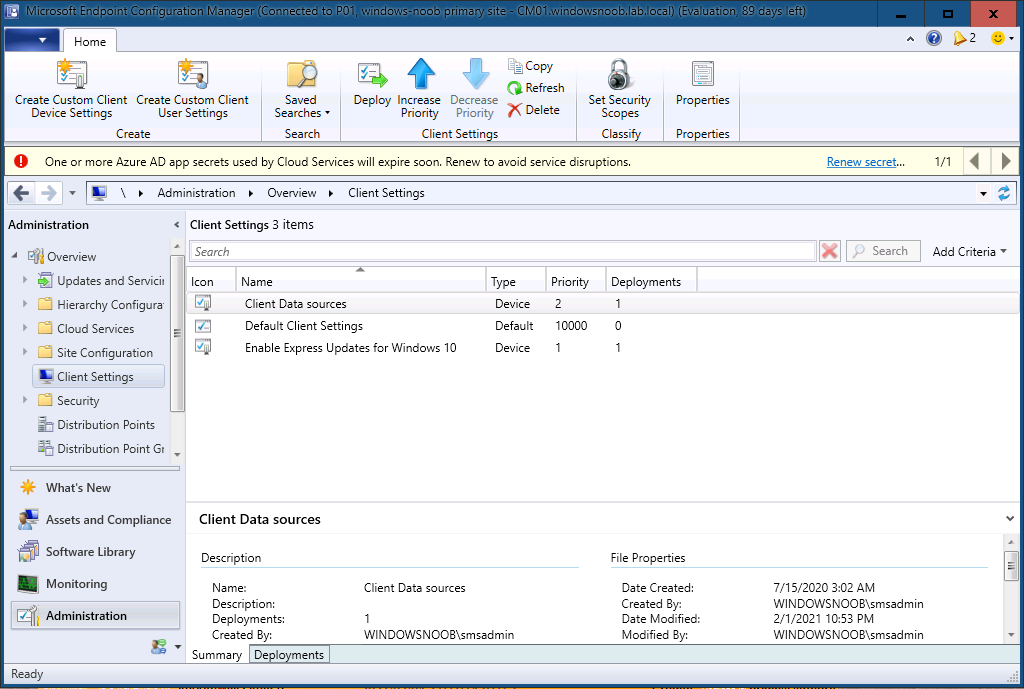
My Technical Preview lab (TP2101) had a message in the ConfigMgr console informing me that:
“One or more Azure AD app secrets used by Cloud Services will expire soon. Renew to avoid service disruption.”
After some quick research I found this.
You need to renew the Azure AD app’s secret key before the end of its validity period. If you let the key expire, Configuration Manager can’t authenticate with Azure AD, which will cause your connected Azure services to stop working.
Starting in version 2006, the Configuration Manager console displays notifications for the following circumstances:
- One or more Azure AD app secret keys will expire soon
- One or more Azure AD app secret keys have expired
To mitigate both cases, renew the secret key.
For more information on how to interact with these notifications, see Configuration Manager console notifications.
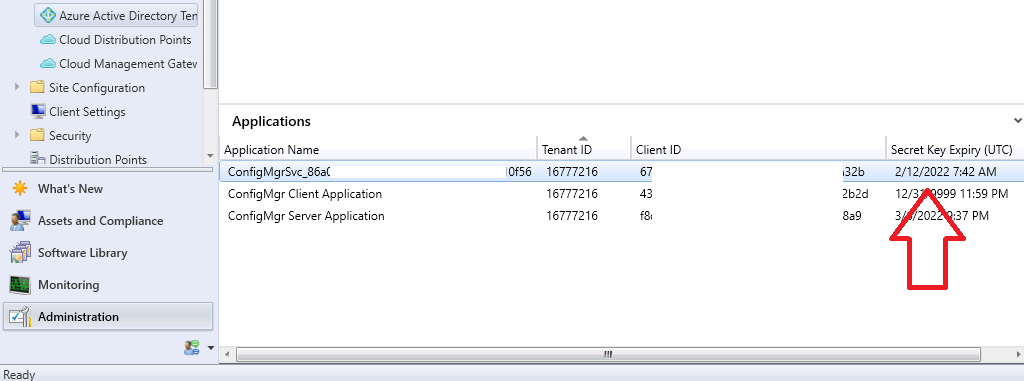
That sounded pretty drastic so I clicked on the Renew secret link in the notification. This revealed my Secret Key Expiry (UTC) dates.
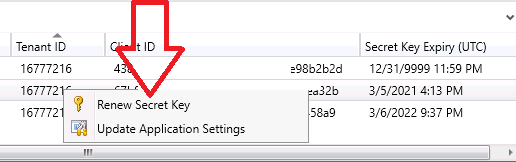
 From there I could right-click on the soon to be expired app and choose Renew Secret Key.
From there I could right-click on the soon to be expired app and choose Renew Secret Key.
 I was then prompted to sign-in to Azure Ad. It listed the account I was already signed in with (SMSMADMIN).
I was then prompted to sign-in to Azure Ad. It listed the account I was already signed in with (SMSMADMIN).
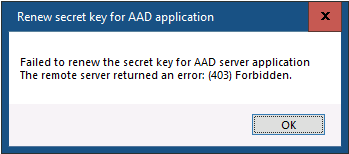
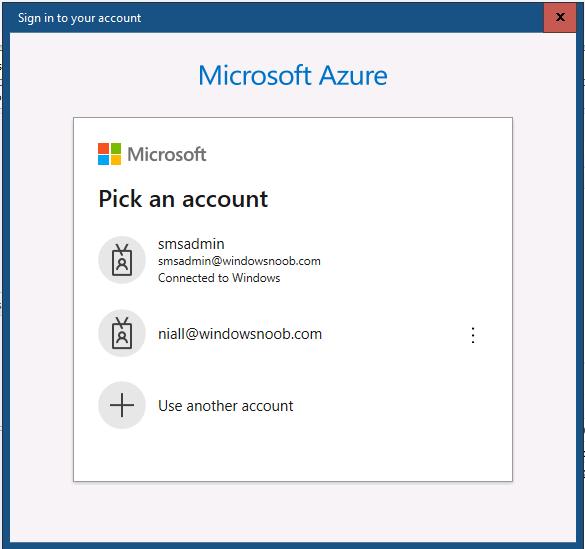 That account has an Intune Administrator role. I then got the following error message.
That account has an Intune Administrator role. I then got the following error message.
“Failed to renew the secret key for AAD server application. The remote server returned an error: (403) Forbidden.”
So I retried the action as an account that had an Azure Global Admin role, this time, all was good.
Note: According to Microsoft here the permissions needed must be via: “Enter the credentials of either the app owner or an Azure AD administrator”
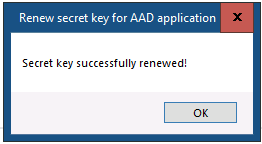 And the new date is shown in the console.
And the new date is shown in the console.
Related reading
- https://docs.microsoft.com/en-us/mem/configmgr/core/servers/deploy/configure/azure-services-wizard
- https://docs.microsoft.com/en-us/troubleshoot/mem/configmgr/cmg-communication-error-403



When I try to renew secret key for two app I have this error:
“Failed to renew the secret key for AAD server application. Failed to get server app”
This because I have deleted these apps from Azure.
Now, how can I delete also from SCCM to hide expired secret key notification on top of console?
Thank you.
Luca