Introduction
Microsoft recently announced that HTTP only communication will be dropped from ConfigMgr in October 2022 here.
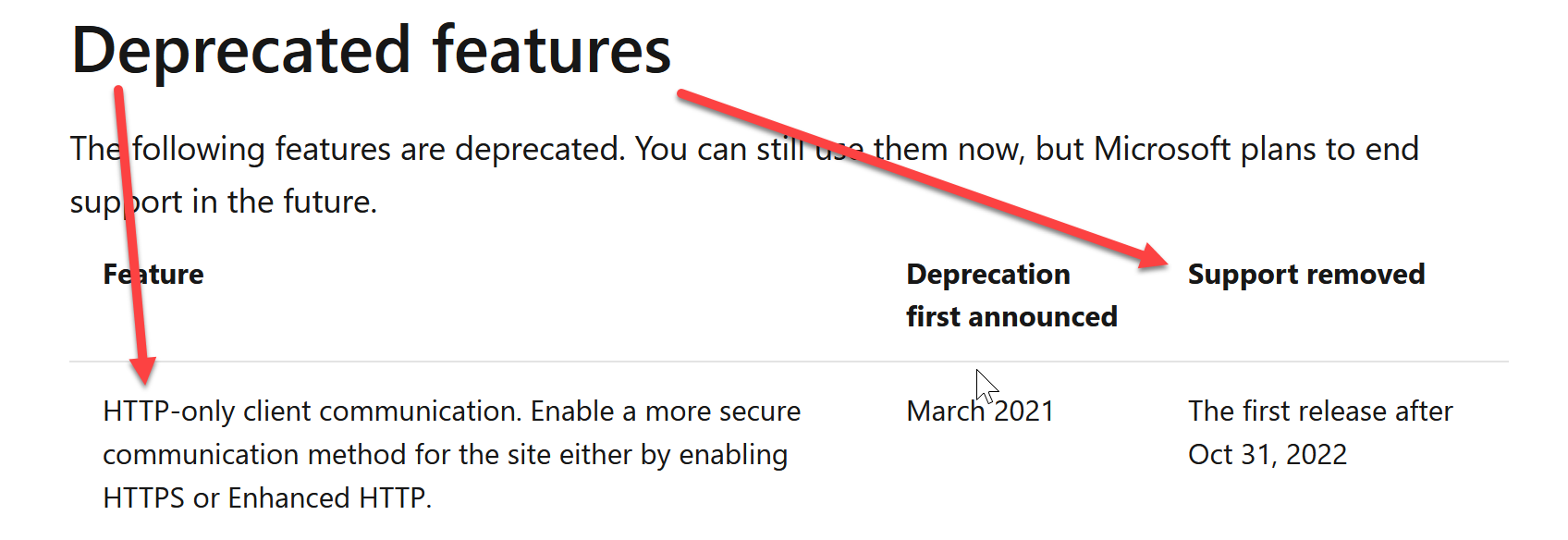 The advice is to enable a more secure communication method for the site either by enabling HTTPS or Enhanced HTTP.
The advice is to enable a more secure communication method for the site either by enabling HTTPS or Enhanced HTTP.
Learn about HTTPS
If you’d like to learn how to setup HTTPS in your lab and convert ConfigMgr from HTTP to HTTPS then please review the following blog posts.
Setup PKI
- Part 1 – Introduction and server setup
- Part 2 – Install and do initial configuration on the Standalone Offline Root CA
- Part 3 – Prepare the HTTP Web server for CDP and AIA Publication
- Part 4 – Post configuration on the Standalone Offline Root CA
- Part 5 – Installing the Enterprise Issuing CA
- Part 6 – Perform post installation tasks on the Issuing CA
- Part 7 – Install and configure the OCSP Responder role service
- Part 8 – Configure AutoEnroll and Verify PKI health
Convert ConfigMgr to HTTPS
- How can I configure System Center Configuration Manager in HTTPS mode (PKI) – Part 1
- How can I configure System Center Configuration Manager in HTTPS mode (PKI) – Part 2
What about enhanced HTTP ?
Check Microsoft recommends before you seriously consider using enhanced HTTP. I draw attention to that in the figure below:
 Microsoft recommends using HTTPS communication for all Configuration Manager communication paths, but it’s challenging for some customers due to the overhead of managing PKI certificates.
Microsoft recommends using HTTPS communication for all Configuration Manager communication paths, but it’s challenging for some customers due to the overhead of managing PKI certificates.
Since ConfigMgr 1810 (first seen in 1806), Enhanced HTTP was made available to fill that gap. For more information see https://docs.microsoft.com/en-us/mem/configmgr/core/plan-design/hierarchy/enhanced-http.


