Introduction
Microsoft released Endpoint Manager Configuration Manager update 2010 this week and it’s available now to install in production using the fast ring method. This release includes many very cool cloud friendly features that were recently show cased in the Technical Preview releases of Configuration Manager.
One such feature is the ability to escrow recovery information to your on premise infrastructure via the Cloud Management Gateway.
I tested this new ability when it first was released in Technical Preview 2010.2 and you can read about that here. But now, it’s available for all to use in production deployments with Update 2010 for Configuration Manager, and it works really well! Over the last few days I’ve tested this over and over to verify the behavior and it works as stated.
As long as you have a working CMG in place, and have upgraded your site and client to Configuration Manager 2010, then you’ll be able to use this new ability.
However there is a gotcha, and that is if you previously created BitLocker Management policy prior to upgrading to 2010 you’ll need to go in and edit the policy prior to testing this, or alternatively create new BitLocker Management policy and that’ll also work.
To see this in action, please watch my video to get details of the process from start to finish.
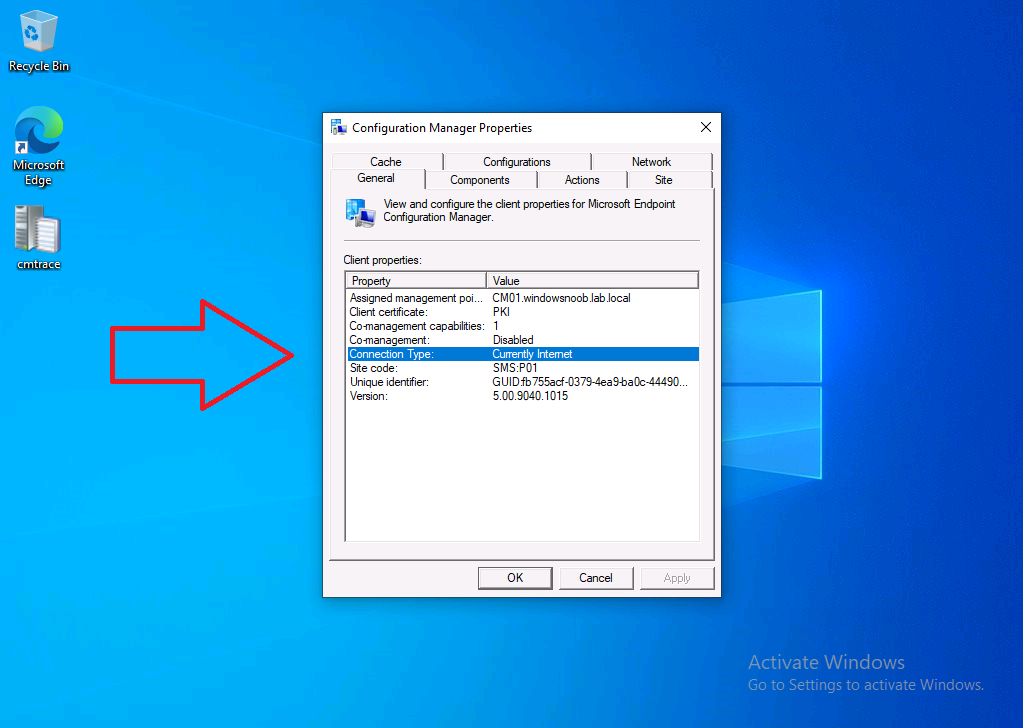
Below you can see my Windows 10 client computer is listed with a connection type of Currently Internet, and in this state it retrieves policy and content from the Cloud Management Gateway.
You can verify the connection type in the C:\Windows\CCM\Logs\ClientLocation.log file. It’ll probably be one of the following:
- Currently Intranet
- Currently Internet
- Always Internet
For this blog post though, we want to simulate a remote work with no access to the Domain Controller or on-premise Management Point, but with a internet connection and thus, a connection to the CMG.
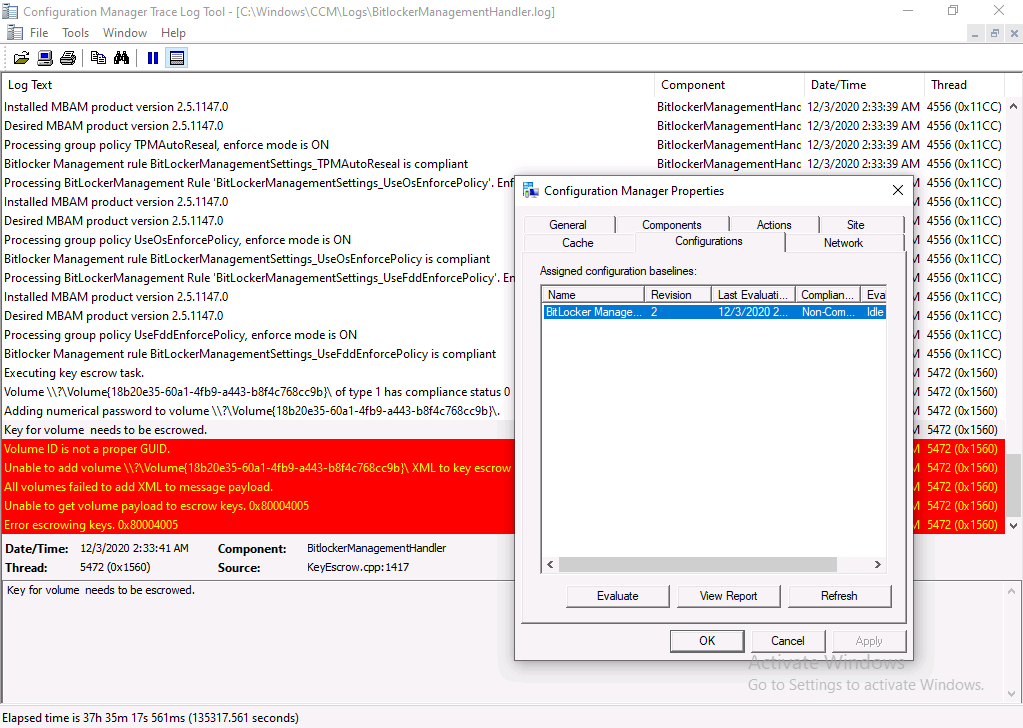
 After receiving BitLocker Management policy from the CMG it starts the process of logging things to the BitLockerManagementHandler.log and it installs the MDOP Agent, which itself starts checking for policy compliance and reports back to the log. In the screenshot below the device has just started processing policy and is still in a non-compliant state.
After receiving BitLocker Management policy from the CMG it starts the process of logging things to the BitLockerManagementHandler.log and it installs the MDOP Agent, which itself starts checking for policy compliance and reports back to the log. In the screenshot below the device has just started processing policy and is still in a non-compliant state.
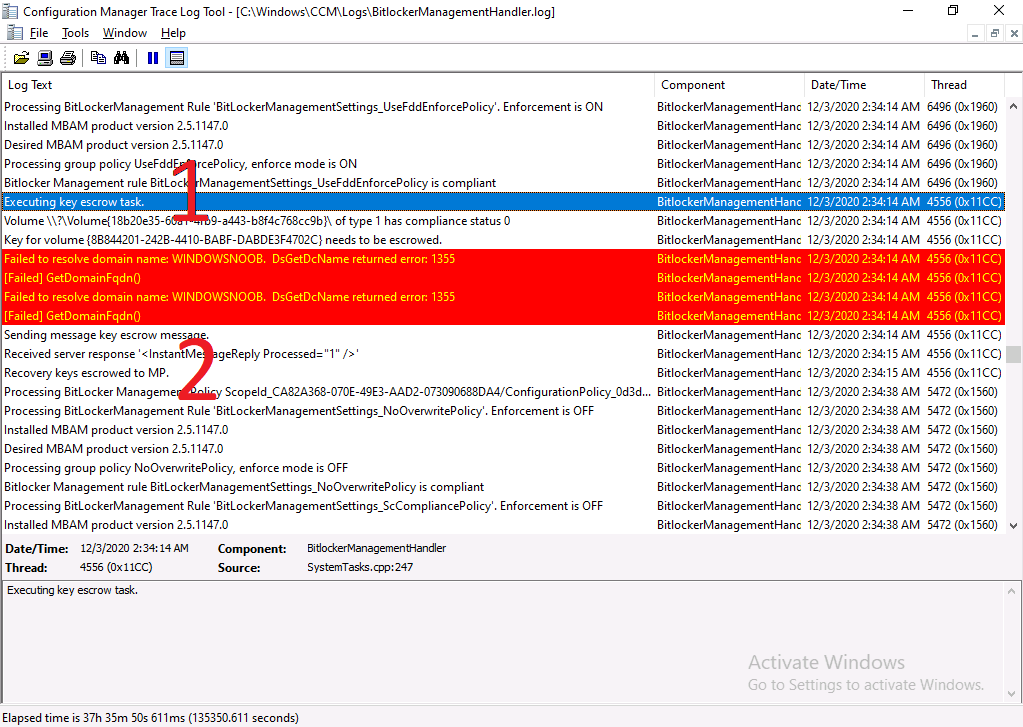
 After a time period defined in your BitLocker Management policy it escrows the recovery keys via the CMG as shown in (1) and receives a response from the server (2).
After a time period defined in your BitLocker Management policy it escrows the recovery keys via the CMG as shown in (1) and receives a response from the server (2).
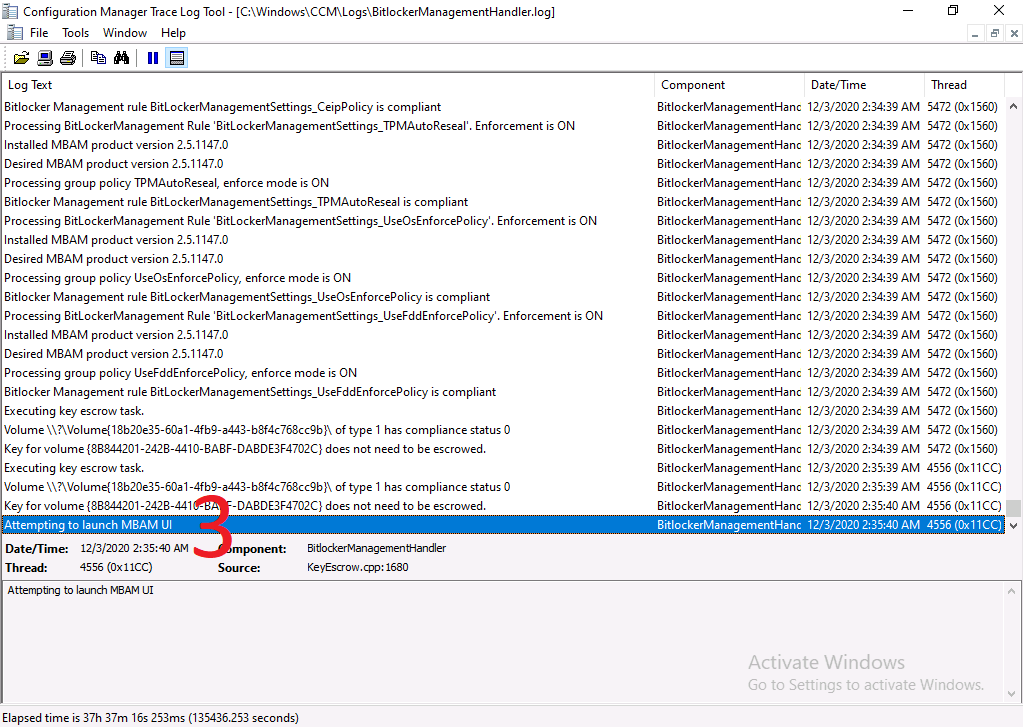
 After the recovery key information has been escrowed via the CMG it launches the MBAM UI to inform the end user that it’s encrypting the drive (3).
After the recovery key information has been escrowed via the CMG it launches the MBAM UI to inform the end user that it’s encrypting the drive (3).
 And that’s it, job done, the device is encrypted via policy delivered from the CMG and recovery information is escrowed via the CMG, all without requiring any connection back to the domain controller or the on premise ConfigMgr infrastructure.
And that’s it, job done, the device is encrypted via policy delivered from the CMG and recovery information is escrowed via the CMG, all without requiring any connection back to the domain controller or the on premise ConfigMgr infrastructure.
“proof that … Microsoft listen to customer feedback and implement features that are needed in a timely and professional manner”
This is amazing !
I hope you try out this new amazing functionality, this feature and many of the other cool new features in update 2010 are proof that the program managers at Microsoft listen to customer feedback and implement features that are needed in a timely and professional manner,
Excellent job Microsoft ! and thanks to Frederic Mokren (PM in PG) for his support.
Please retweet this !
cheers
niall



Pingback: Microsoft Cloud ve Datacenter Management Aralık 2020 Bülten – Sertaç Topal