In Part 1 of this mini series we integrated Windows Intune with System Center 2012 R2 Configuration Manager. In Part 2 we added Support for iOS devices (Iphone, iPad). In Part 3 we learned the difference between App Package for iOS (*.ipa file) and applications from the Apple App Store. We learned how to deploy them to iOS devices and configured the deployment type so that the applications were made available to the user based on the iPhone or Ipad operating system version, in addition we also checked device Ownership information and deployed the application based on those requirements.
In Part 4 we learned how to use and configure compliance settings in order to enable or disable certain configurable features on iOS devices. We enforced a Password requirement and enforced a minimum password length as this is a common requirement for organizations. In Part 5 we enabled support for Windows 8.1 devices (both Windows RT 8.1 and Windows 8.1 Enterprise) so that they could be managed via System Center 2012 R2 Configuration Manager integrated with Windows Intune. Now we will look at deploying Windows 8.1 apps (appx) to Windows 8.1 devices.
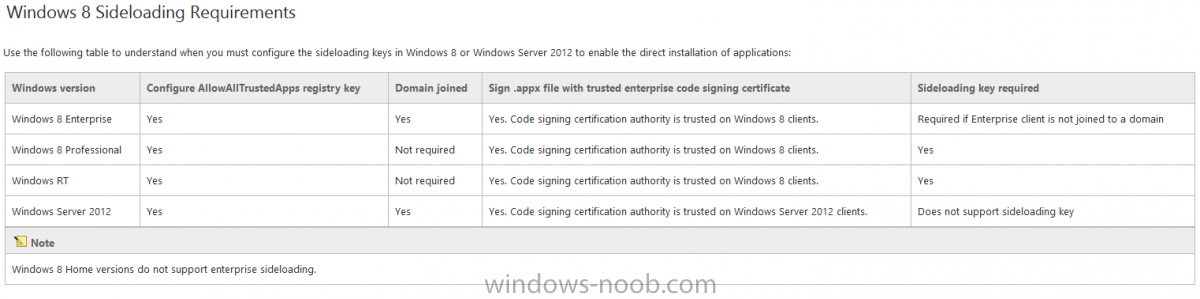
Mobile apps that are deployed using Configuration Manager appear in the company portal on mobile devices. You can deploy sideloaded apps or links to application stores to enrolled devices. Client computers that run different versions of Windows 8 have different requirements for enabling the sideloading of apps. For example, you must configure the sideloading key on a computer that runs Windows 8 Enterprise if the computer is not joined to a domain. For more information about these requirements, see the following section in Technet:- Windows 8 Sideloading Requirements.
Note: In case it’s not clear in the table below, if you want to sideload apps you need a sideloading key. To create a sideloading key expand Software Library, Application Management, Windows Sideloading Keys and right click, choose Create SideLoading key and enter the details. For the purposes of this guide I will assume that you have entered your sideloading key(s) prior to commencing the steps below.
You can enable sideloading for this scenario by installing a sideloading product key on the computers. For more information about sideloading product activation keys, see Microsoft Volume Licensing. Additionally, the article How to Add and Remove Apps describes how to use the Windows Software Licensing Management Tool (Slmgr.vbs) to add and activate the sideloading product key.
Step 1. Create a Reg key to allow Appx installation
First of all we need to configure Windows 8 computers to allow direct installation of Windows 8 apps (appx apps). To do so, you would normally use group policy to configure the following sideloading registry settings, however our Windows 8.1 devices are not domain joined so Group Policy is out of the question. As we cannot currently deploy registry entries via Windows Intune integrated with Configuration Manager you’ll need to do this step manually or use a script.
As our (modern) Windows 8.1 devices are workgroup joined we need to manually create the following registry key, so please save the text below into a file called AllowAllTrustedApps.reg and then run it on your Windows 8.1 clients.
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Appx] "AllowAllTrustedApps"=dword:00000001
Step 2. Create and deploy a Certificate Profile
A Certificate is required to ensure that the app is trusted. Without the correct certificate, you can’t sideload apps. As we will be installing an Appx app using the Company Portal we therefore need the certificate in place.
Tip: Sideloading of apps is when you install them using a method other than the via the Store (sideloading is appropriate for other platforms as well, such as iOS, Windows Phone, Android).
This certificate does not have to be rooted to a trusted certification authority; it just has to be trusted by your PCs. The Publisher Name in the package manifest must match the Publisher Name in the certificate that is used to sign the app package. Windows trusts many Certificate Authorities without any additional configuration. If the certificate is from one of these already trusted authorities, you don’t need to deploy and manage additional certificates to the targeted PCs. You also can use your company’s internal Certificate Authority to sign the app, as long as you ensure that the CA certificate is installed in the Windows images of the targeted PCs.
We can use a new feature in Configuration Manager 2012 R2 to deploy Certificate Profiles. Certificate profiles in System Center 2012 Configuration Manager works with Active Directory Certificate Services and the Network Device Enrollment Service role to provision authentication certificates for managed devices so that users can seamlessly access company resources. For example, you can create and deploy certificate profiles to provide the necessary certificates for users to initiate VPN and wireless connections.
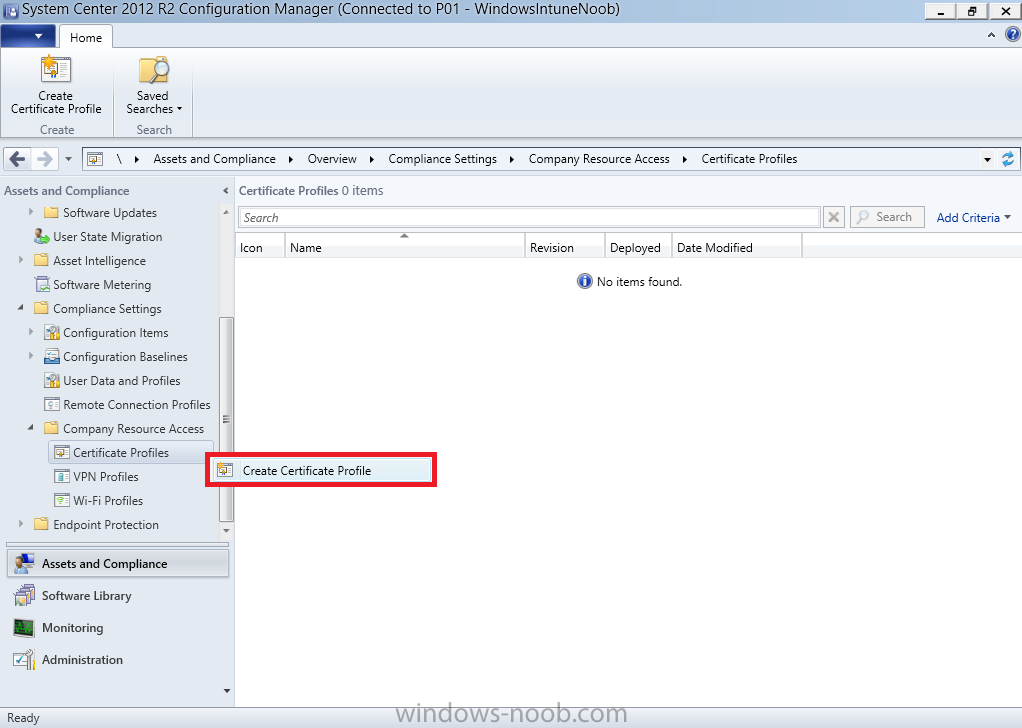
In Assets and Compliance expand Compliance Settings, then expand Company Resources and finally select Certificate Profiles. Right click and choose Create Certificate Profile
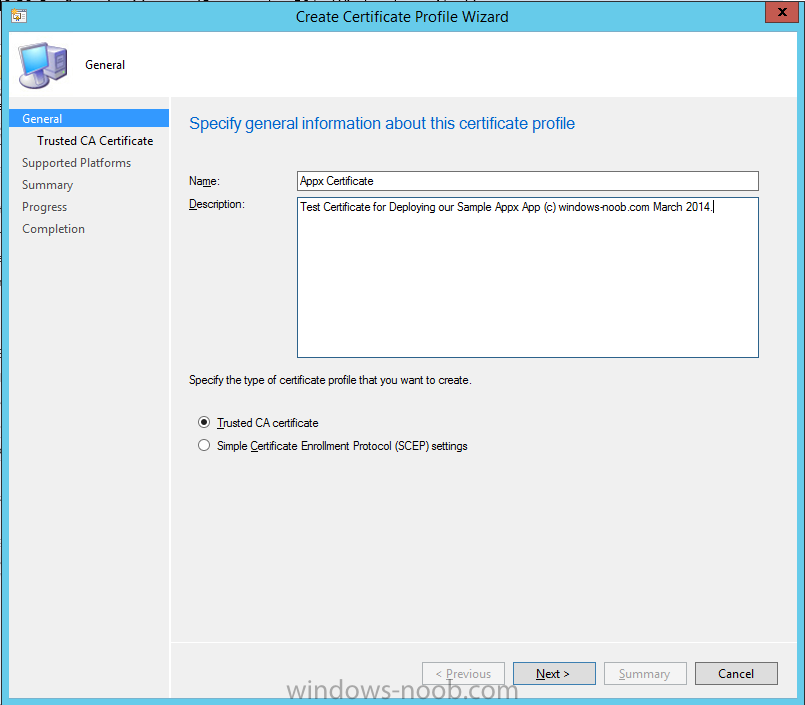
Give it a suitable name and description, In this blog post you are learning how to Deploy Appx apps to modern (mobile) devices and this example will be sufficient for our needs, we can use the certificate we created when we created out sample Appx app in this post.
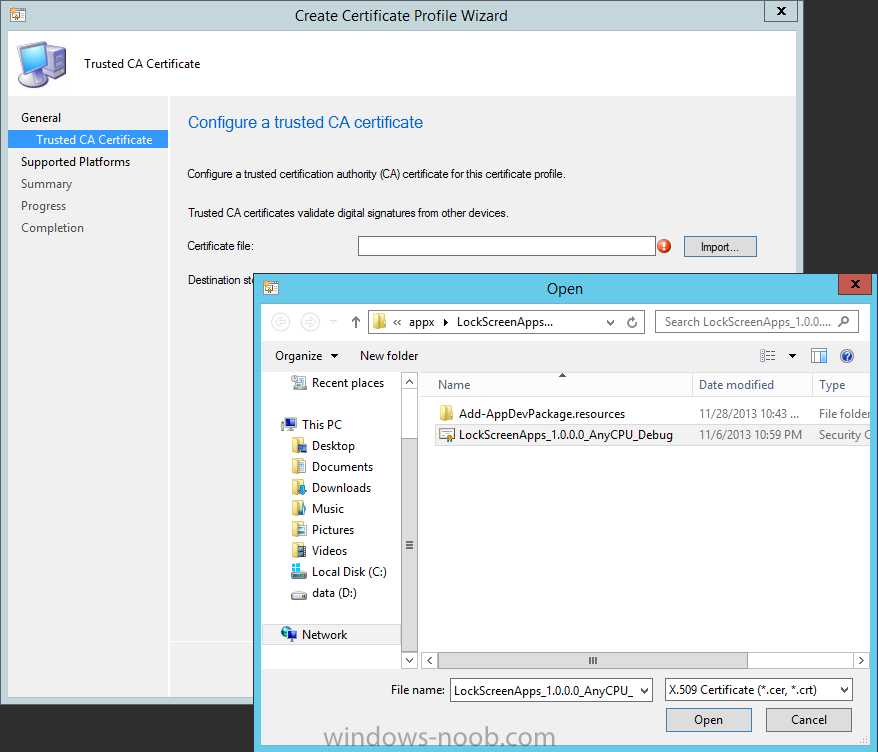
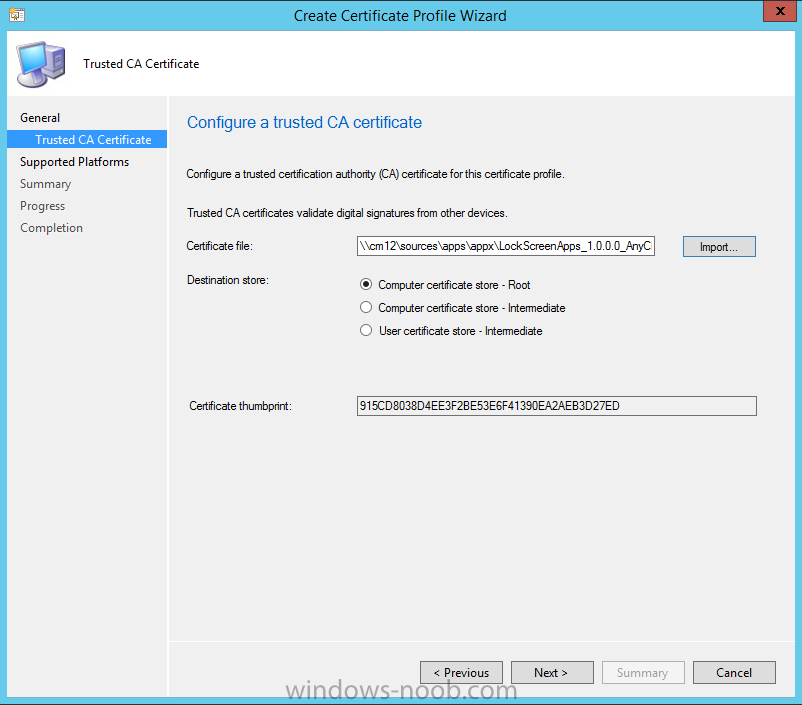
Browse to the folder where you’ve got your Appx certificate (or to the folder where you have a Windows 8.1 appx app source files plus the self signed certificate) and select the certificate and then choose open.
We can use the default Computer Certificate Store (Root)
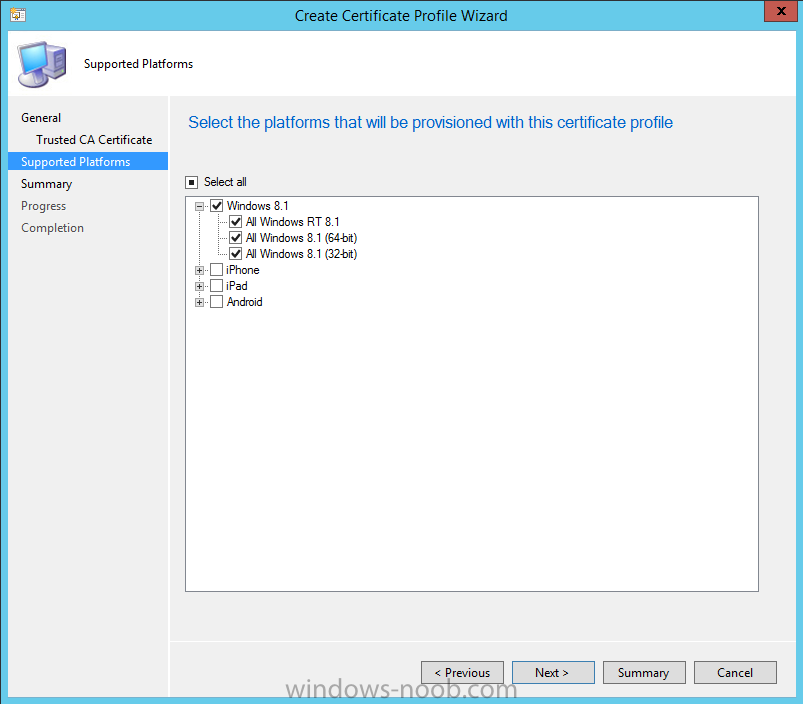
Next we want to select the Operating Systems we want to provision with this certificate profile, so select Windows 8.1
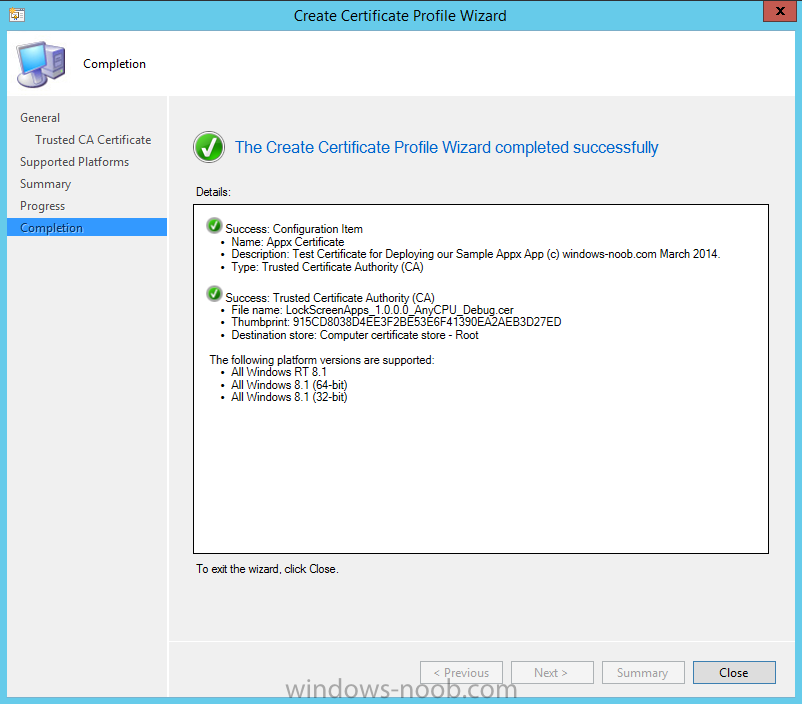
The certificate profile is created, click close.
Step 3. Deploy the Certificate
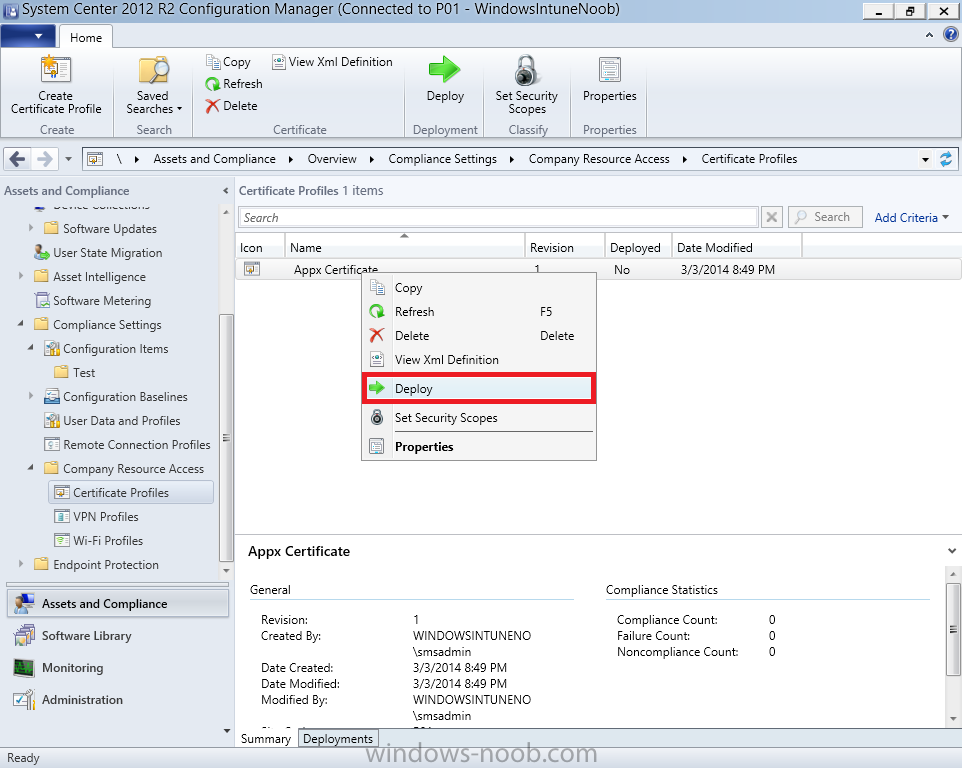
Now that we’ve created our test appx certificate profile, we will deploy it to our Windows 8.1 modern devices. Right click the certificate profile and choose Deploy.
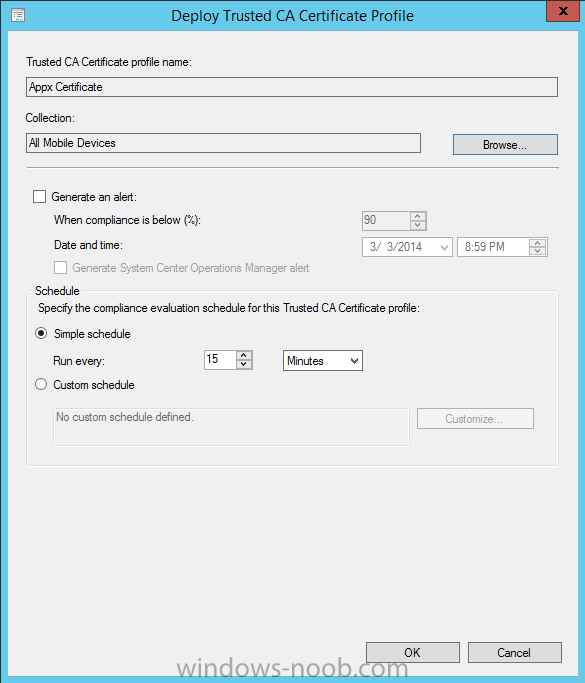
and select the All Mobile devices Device collection.
Note: In the screenshot below I have not changed the compliance evaluation schedule from the default setting of 15 minutes, which in a lab is ok, however in production you’d want to set it to something more realistic like once a week.
Step 4. Verify the Certificate is deployed
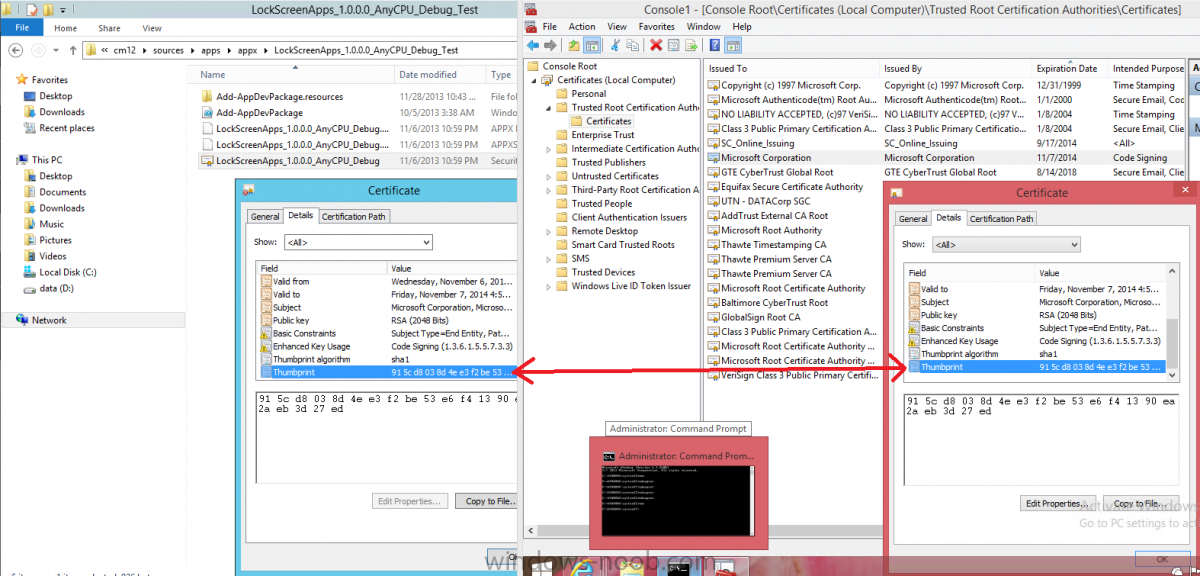
Now that the Certificate is deployed it’s a waiting game, the device must receive it’s policy which by default is once every 24 hours. Once it has received policy you can verify that the certificate is actually deployed by bringing up the Certificates MMC on one of your Windows 8.1 devices. In the screenshot below we are viewing a certificate on two separate computers, the one on the left is on the CM12 server and the one on the right is on a Windows 8.1 client. On the left side you can see the Certificate properties of the self signed certificate in the sample Appx app highlighted, you can bring up the Certificate Properties by double clicking on the certificate in the sample Appx folder, and on the right side we have the Certificate Properties of the Certificate we Deployed to our Windows 8.1 device in Step 3 above. If you look closely, they match.
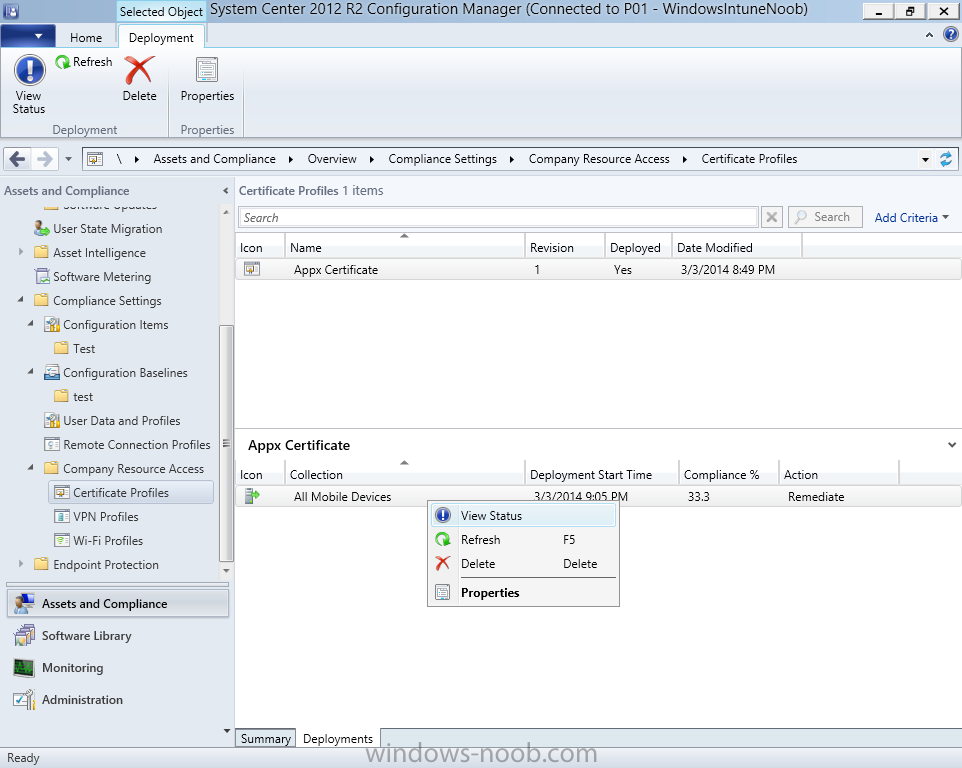
Additionally you can browse to the Deployments tab of our Appx Certificate deployment, and right click and choose View Status
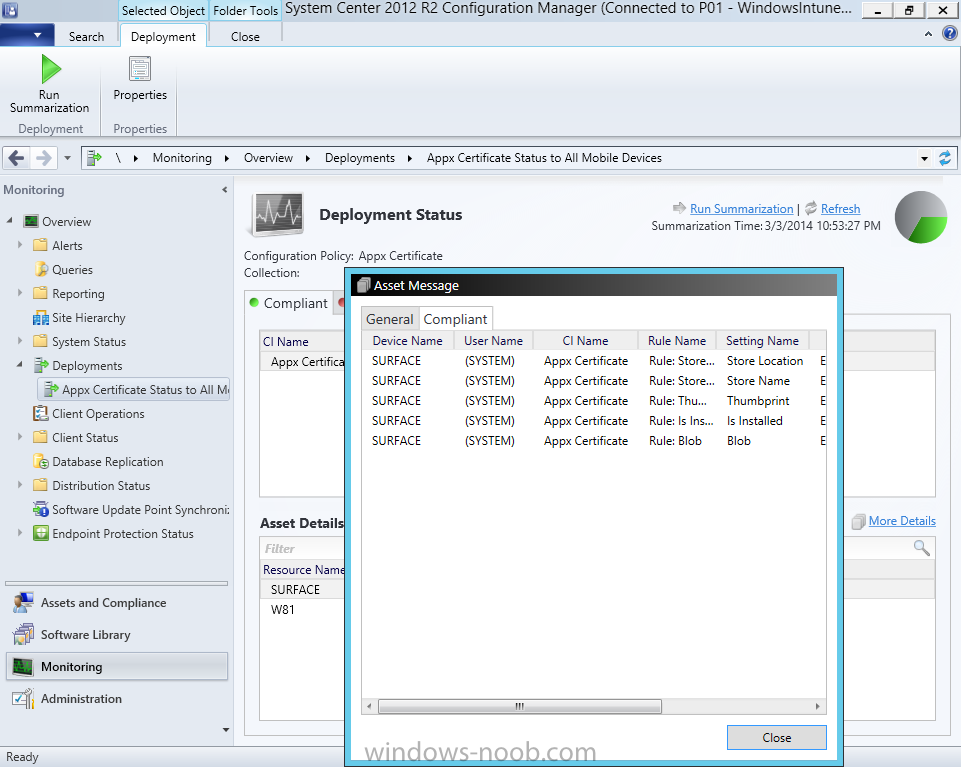
which will bring you to the monitoring node and allow you to dig deeper in terms of successful deployments etc, the screenshot below shows the successful deployment of the certificate used above on one of the 3 Windows 8.1 devices used in this lab.
Step 5. Create an Appx App
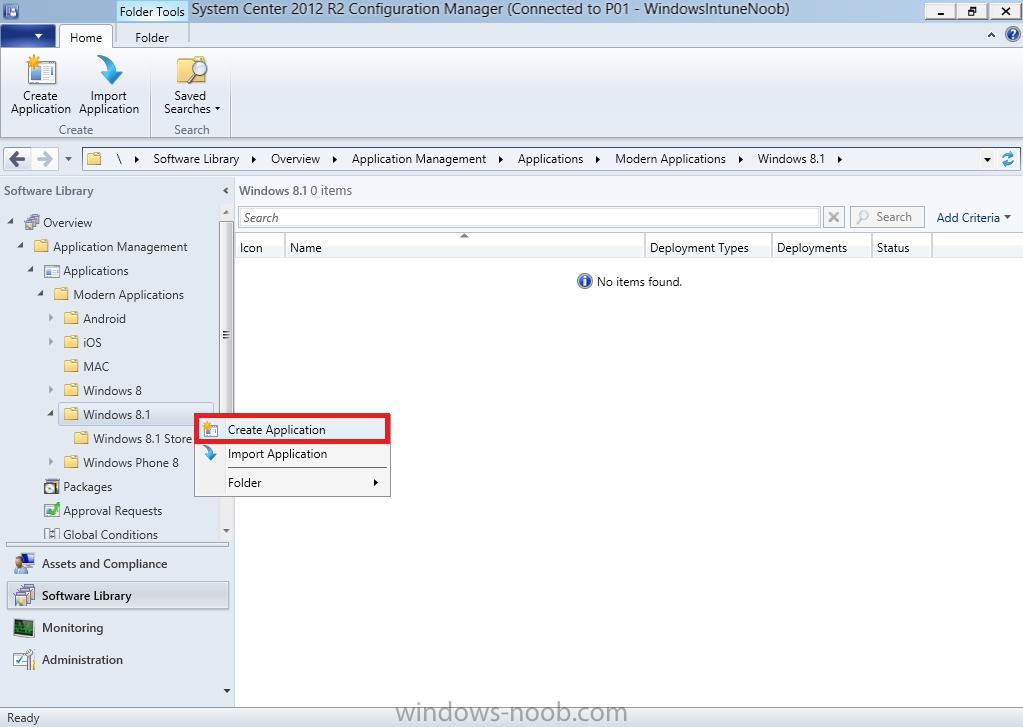
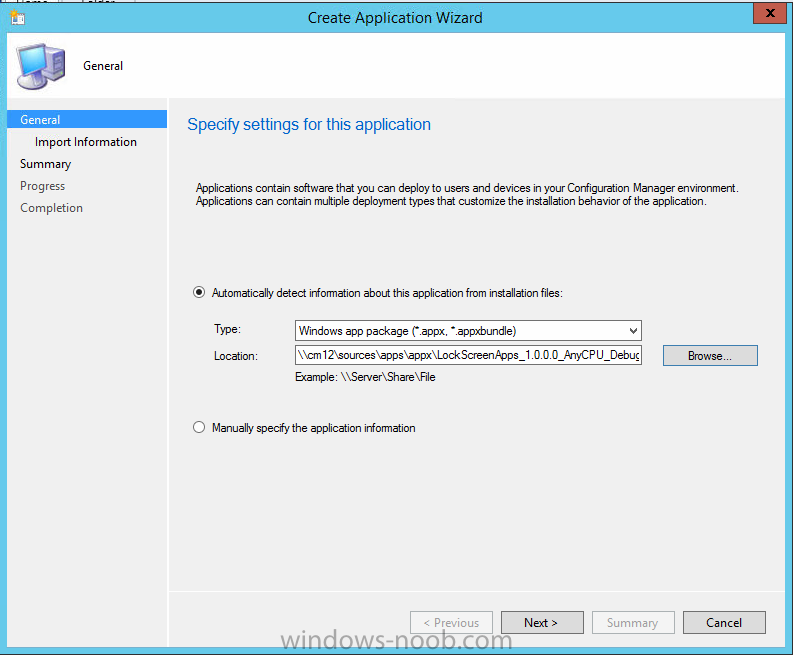
In Application Management, Applications, section browse to our previously created folder layout and select Windows 8.1, right click and choose Create Application, select Windows Appx package from the type menu (the default is MSI)
point it to our sample app that we created earlier
and fill the UNC location of the appx app
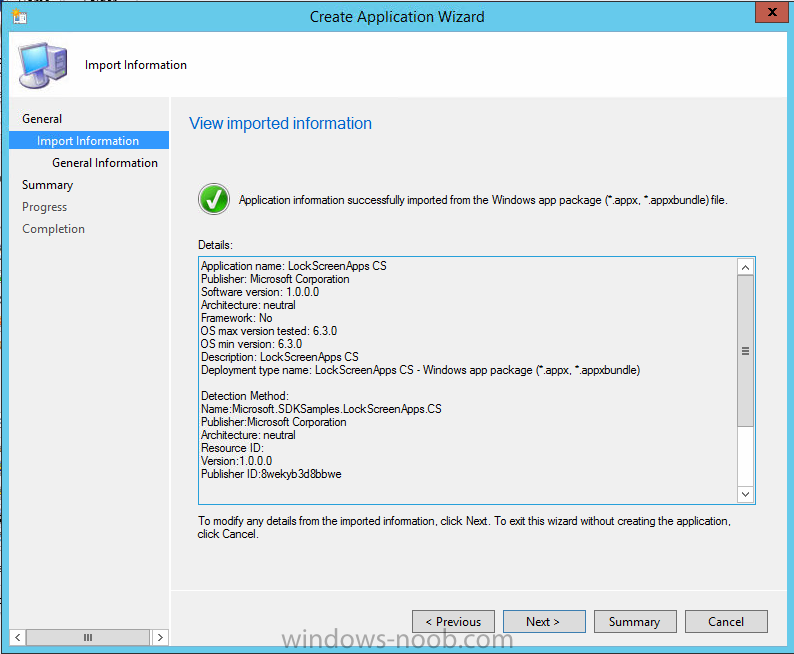
the import information is shown
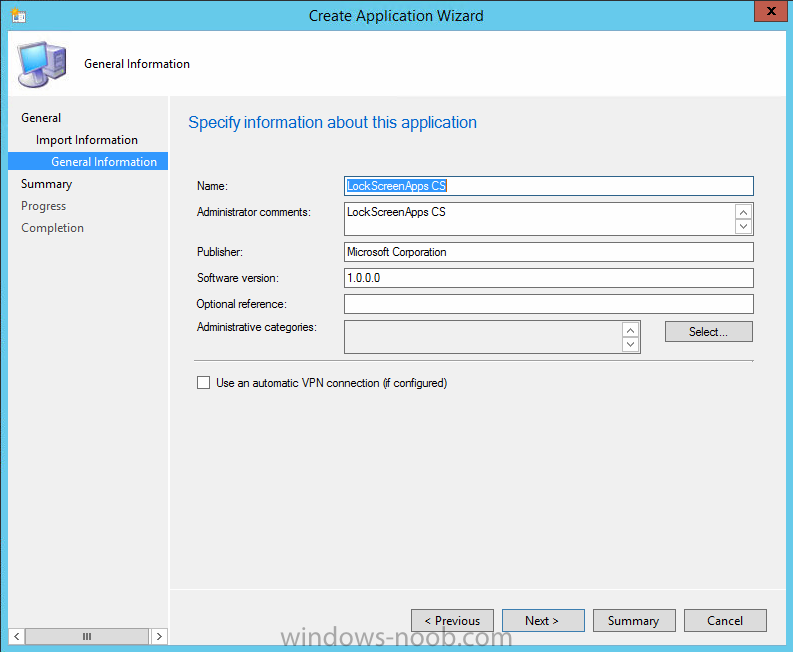
On the General Information screen add any changes you need or just click next to continue, note that you can also select to Use an Automatic VPN connection (if configured), this feature is explained here.
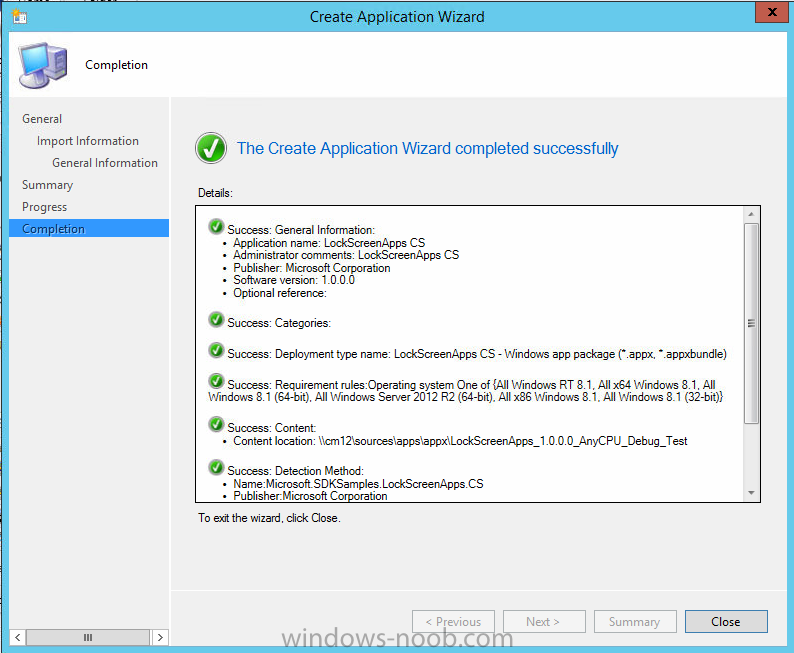
continue through to completion and then close the wizard
Step 6. Distribute The Content
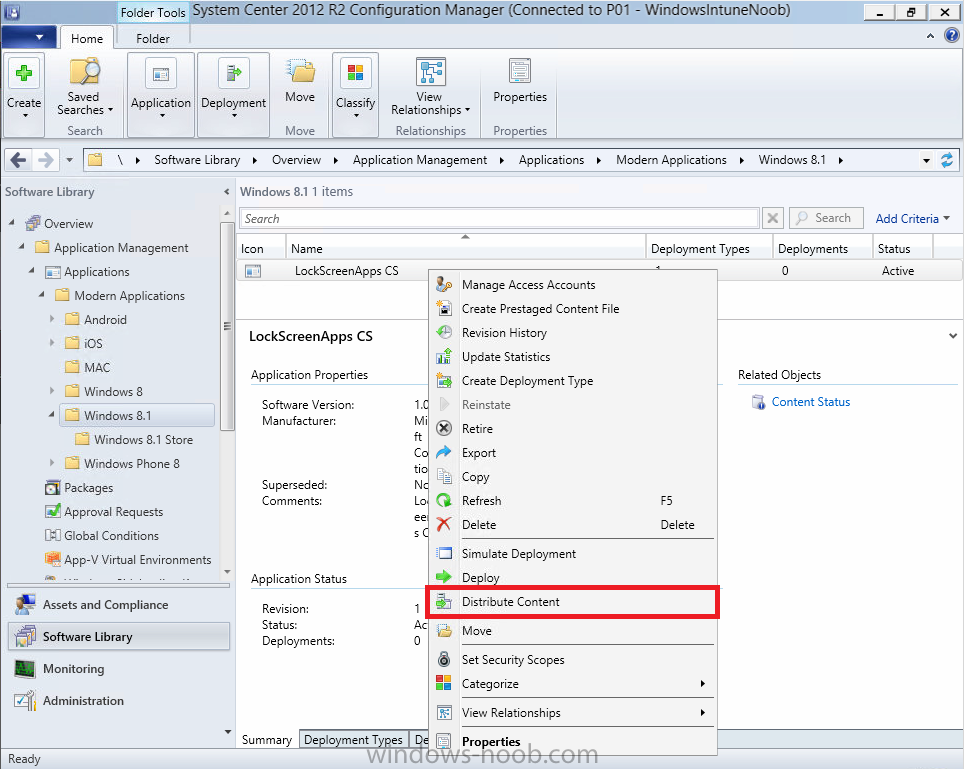
Modern devices (and other clients too) won’t be able to get Appx apps unless the content is actually present in the ‘cloud’ so we need to distribute it to our Windows Intune managed distribution point. Right click on the newly added Appx app and choose Distribute Content
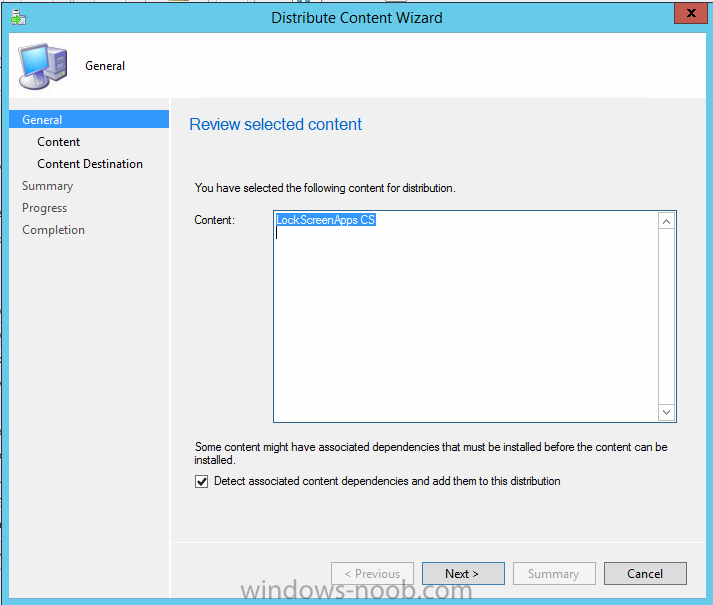
click next
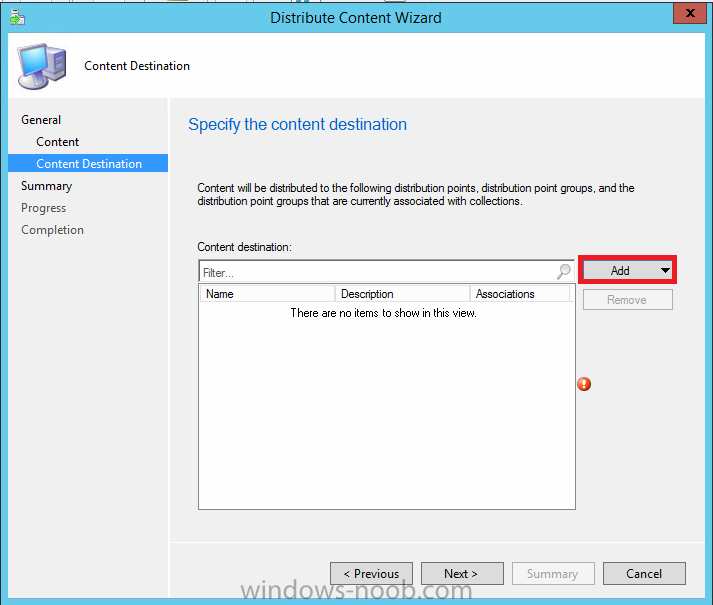
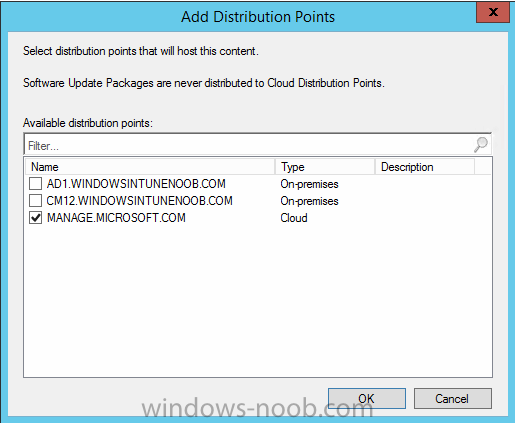
click through to the Content Distribution screen and click on Add to Add a distribution point
select the MANAGE.MICROSOFT.COM distribution point (Cloud)
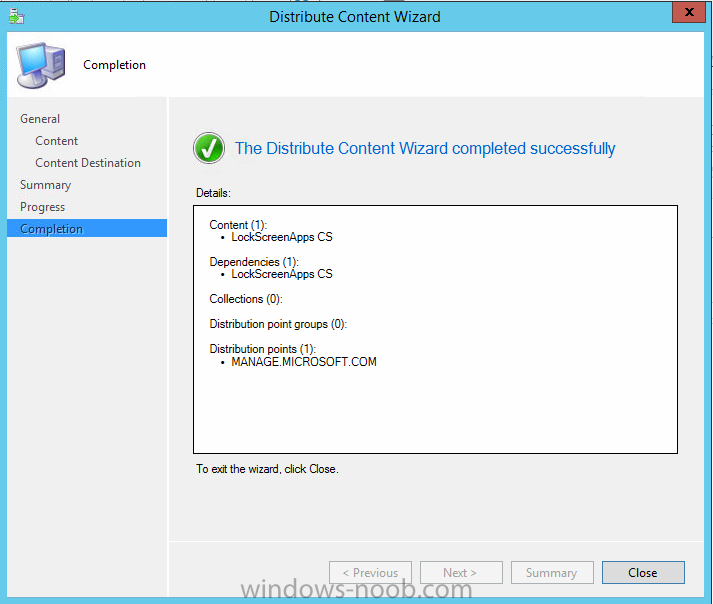
and click your way through the rest of the wizard, you can review the distmgr.log to verify it has distributed the content.
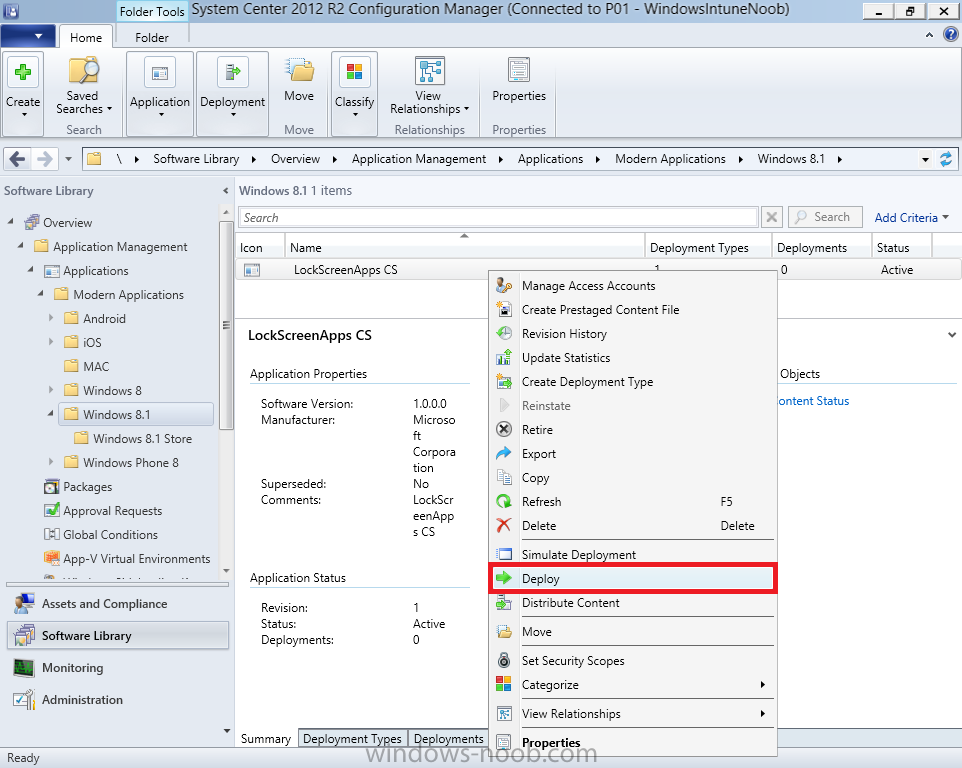
Step 7. Deploy the Appx application
The next step is to Deploy the Appx application in order for our modern device users to see it in the company portal, so right click it and choose Deploy
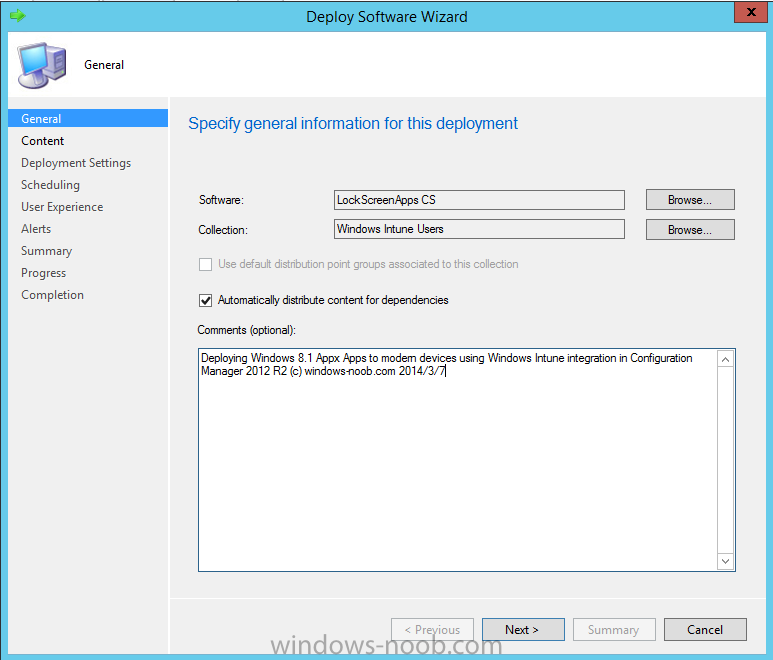
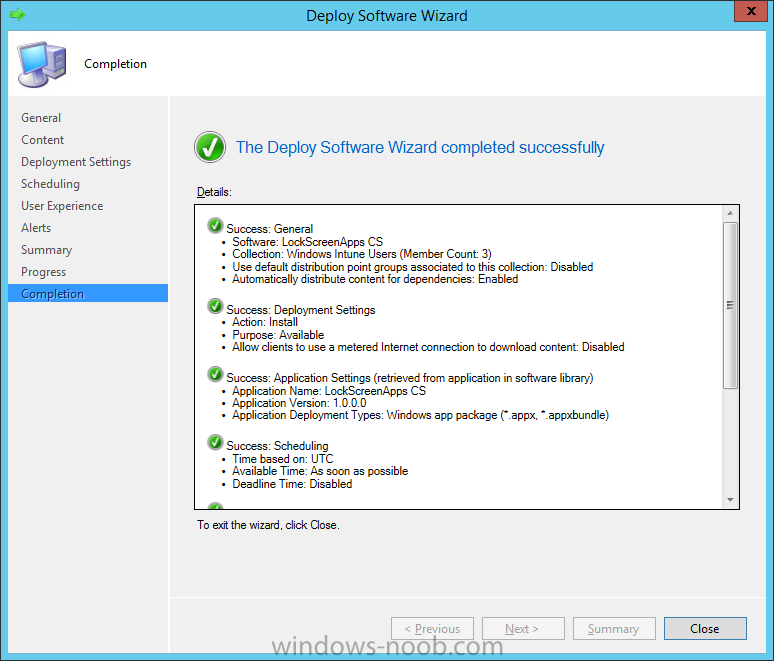
fill in the relevant info and choose the Windows Intune Users collection
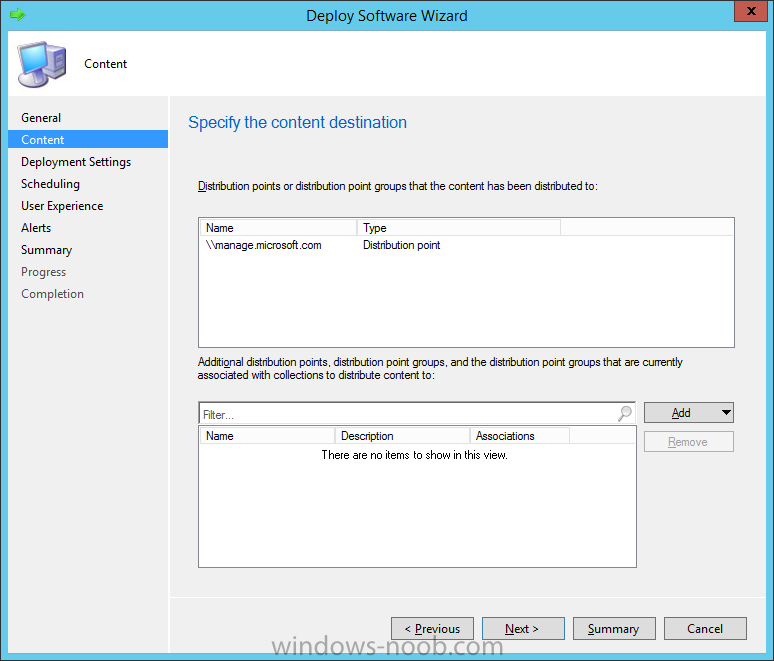
next you’ll see which distribution points the content is on,
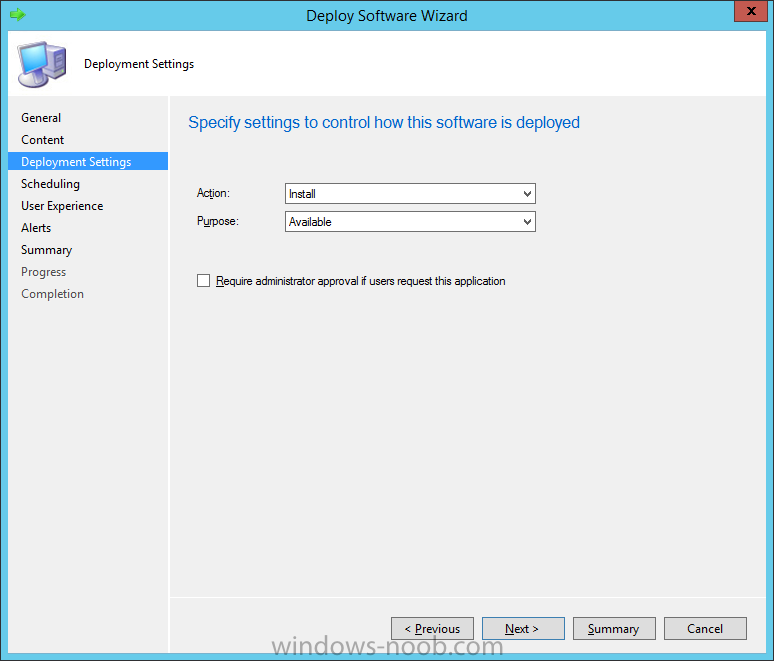
we want the deployment to be of an Available purpose (optional)
click your way through to the end of the Wizard
Step 8. Test the Appx Deployment
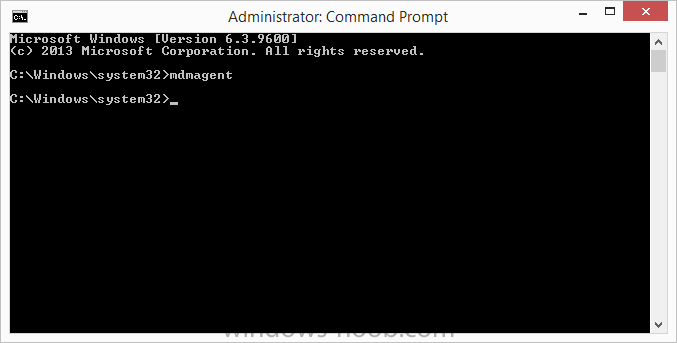
Login to a Windows 8.1 computer that you’ve enrolled exactly as described in Part 5. We will speed up policy retrieval by opening a command prompt and issuing a command called mdmagent
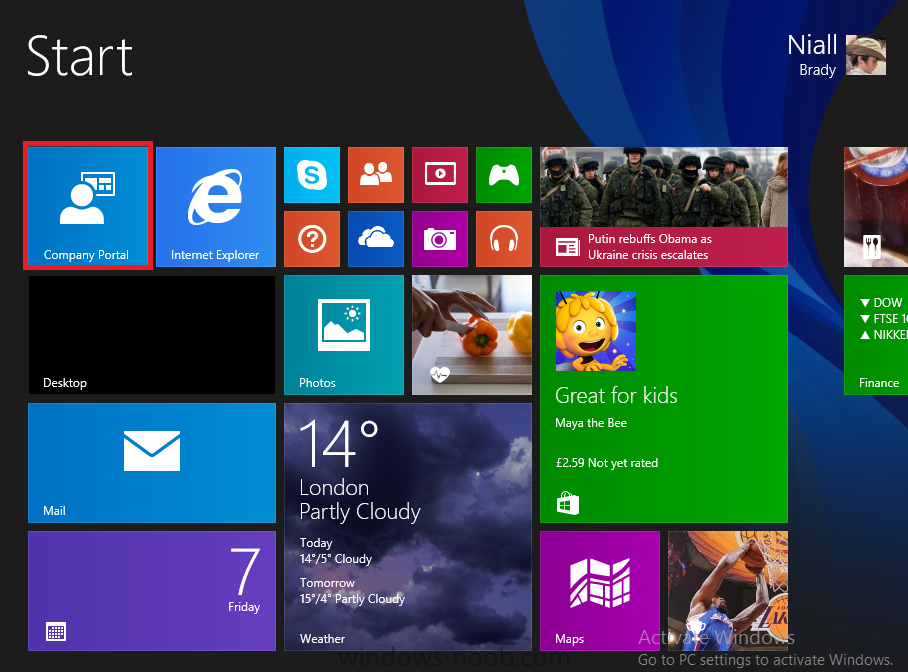
Bring up the Start menu and select the Company Portal
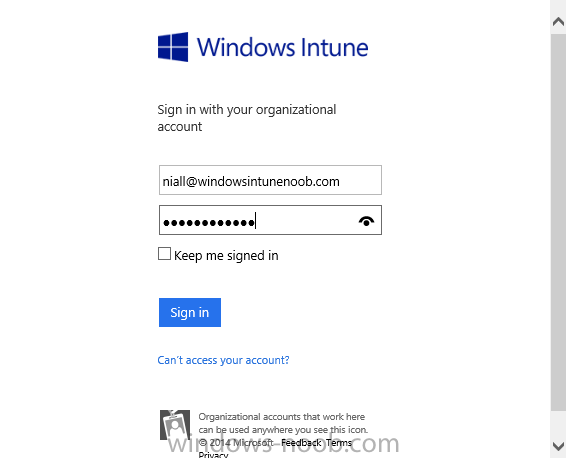
and sign in with your credentials
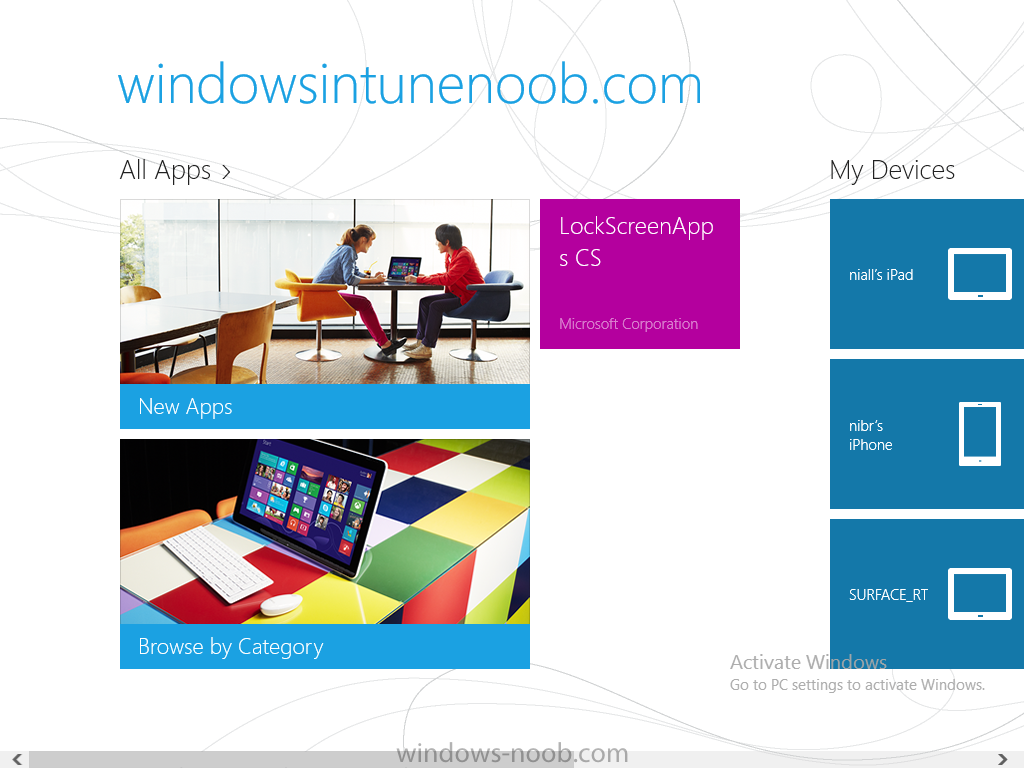
the Lockscreen Appx app appears, click on it to start the installation process
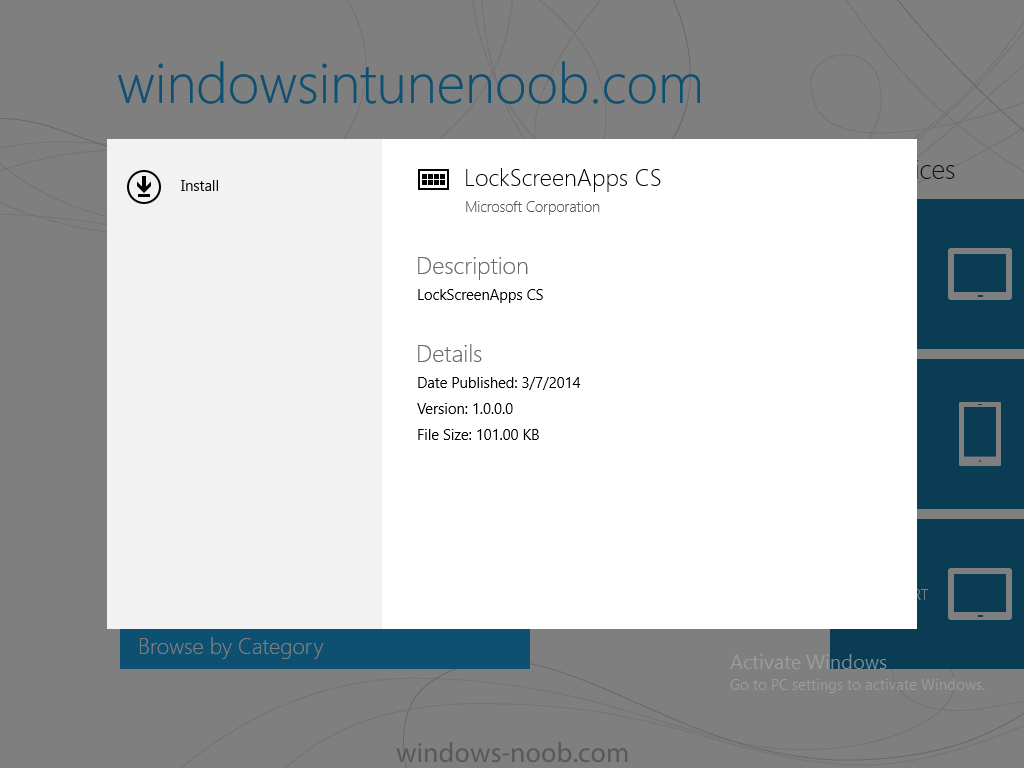
and select Install in the top left corner
it should say Installing
and if everything is ok it will install.
Note: I do not have any sideloading keys and therefore cannot show you the completion of this appx installation.
Troubleshooting
Check the following registry key on your Windows 8.1 device to see the status of your Appx installation
HKEY_Current_User\Software\Microsoft\Windows\CurrrentVersion\MDM\JobDB
and verify the status such as in the screenshot below, the status of 78(120) means SideLoading key is required, to get a list of what these status codes mean see this post.
You can also check that the .appx application has been signed by the correct authority. To do this, make a copy of the appx app, and rename the copied .appx file to .zip and unzip the files. Open the AppxManifest.xml within the extracted files using notepad and check both the Identity parameter and Publisher value.
Recommended Reading
- How to Create and Deploy Applications for Mobile Devices in Configuration Manager – http://technet.micro…ibrary/dn469410
- Windows 8 Licensing Guide – http://download.micr…nsing_Guide.pdf
- Try It Out: Sideload Windows Store Apps – http://technet.micro…s/jj874388.aspx
- Planning to Deploy Windows 8 Apps in Configuration Manager – http://technet.micro…y/jj822984.aspx
- Introduction to Certificate Profiles in Configuration Manager – http://technet.micro…y/dn248971.aspx
- Configuring Certificate Profiles in Configuration Manager – http://technet.micro…y/dn270539.aspx
- Deploying enterprise apps – http://msdn.microsof…s/jj657971.aspx
- Introduction to VPN Profiles in Configuration Manager – http://technet.micro…y/dn261208.aspx
- Troubleshooting Windows RT Client Software Distribution Issues – http://blogs.technet…ion-issues.aspx
- Signing an app package (Windows Store apps) – http://msdn.microsof…(v=vs.110).aspx
Summary
Installing Appx apps on Windows 8.1 devices using Windows Intune Integration in Configuration Manager 2012 R2 is not as straightforward as you would think, there are quite a few requirements on the client which in some cases need to be resolved outside of Configuration Manager/Windows Intune due to current capabilities. However once those requirements are in place you can use the Company Portal as your online ‘store’ in the cloud and manage everything via System Center 2012 R2 Configuration Manager.
Special thanks to Wally and Panu for their advice on this guide.
until next time,
cheers
niall.